Nov 23, 2019 | anonymity, automation, Big Data, Big Tech, Big Tech, Business, Business Email Compromise, Computers, Consumer, cyberattacks, Data, data sharing, Data Storage, Databases, Encryption, Hackers, Hacking, Hacking, Hacking, Internet, Liability, Machine Learning, Monitoring, Radio Show, Radio_Show, Resources, Security, Software, Technology
Big Data, Data Brokers and Your Information Big Data brokers collect our data and establish “hidden” ratings about us before selling it to those who will pay. This information is used by marketers, insurance companies, credit companies, and merchants. ...

Nov 23, 2019 | Applications, Big Tech, Business, CEO, Computers, cyberattacks, Government, Hacking, Hacking, Internet, Microsoft, Microsoft, Microsoft, Radio Show, Radio_Show, Ransomware, Ransomware Attack, Security, Technology, Windows (Microsoft)
Tackling Ransomware on Windows Microsoft has 1 billion Windows-OS powered PCs in use worldwide which explains why they are such a big target for hackers. There are a number of Windows security threats that everyone needs to be aware of including potentially...
Nov 23, 2019 | Android, Android, AT&T, Audio, Big Tech, Business, Cell Phone, cell phones, Cellular Services, Fines and Penalties, Internet, iOS, iPhone, Mobile, Networking, Patching, Phone, Radio Show, Radio_Show, Security Alerts, Smart Phone, Technology, Updates
Cellular Throttling and Why it cost AT&T a Chunk of Change We are all familiar with cell carriers and their different plans — some of which seem to change as fast as the weather in New England. All of them have some type of an ulimited plan —...
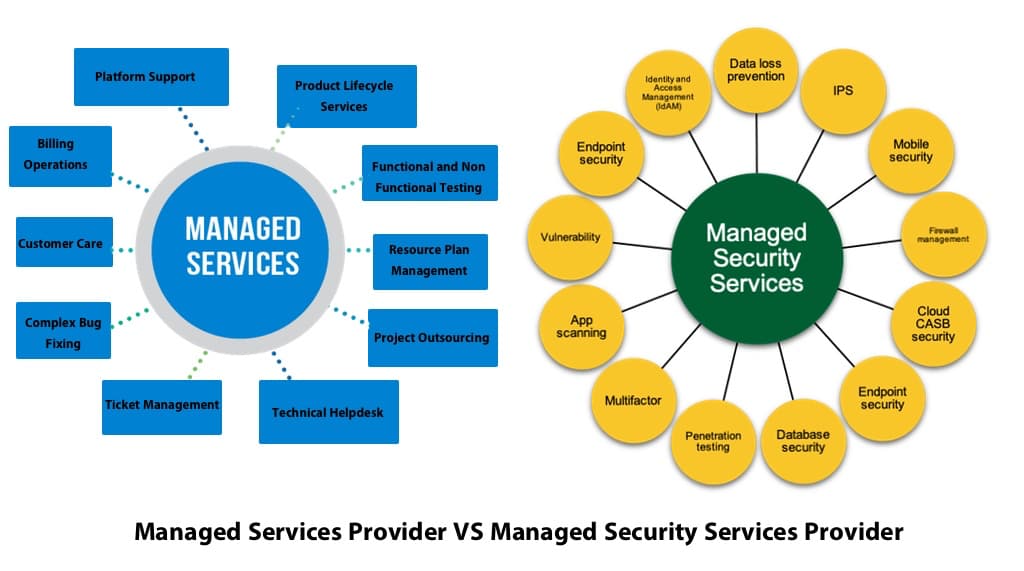
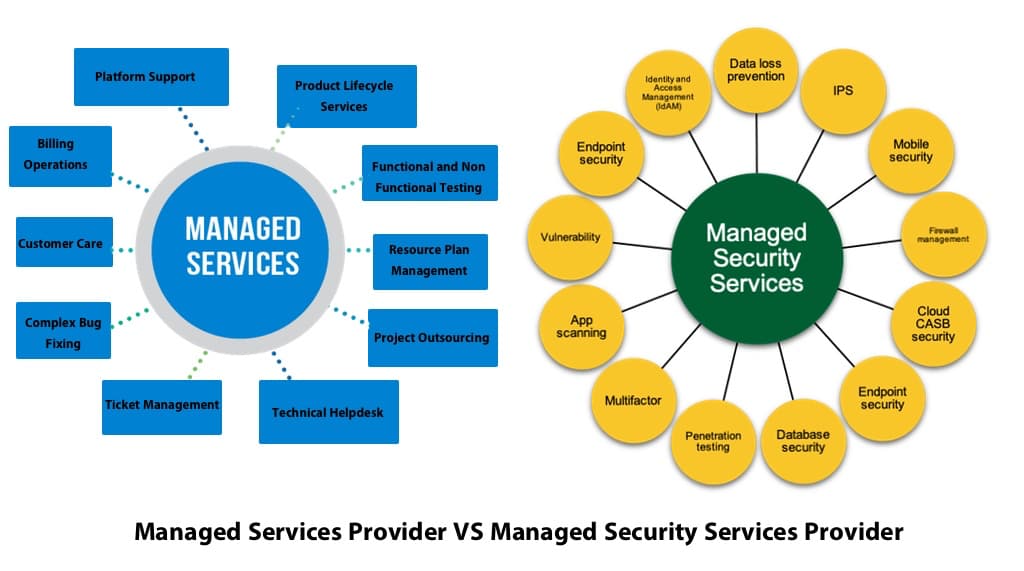
Nov 23, 2019 | Business, Computer Repair, Computers, Disaster_Preparedness, Employment, Facebook, Google, Internet, Internet Service Providers, LinkedIn, Managed Security Services Provider (MSSP), Managed Services Provider (MSP), Networking, Operating Systems, Privacy, Radio Show, Radio_Show, Remote Repair, Security, Technology
The hanging of an MSP “Shingle” and Your Business Security Are you in the cross hairs of hackers? How can a hacker multiply his efforts? By attacking a company who protects other companies. Hackers new targets are the Managed Services providers (MSPs) because...
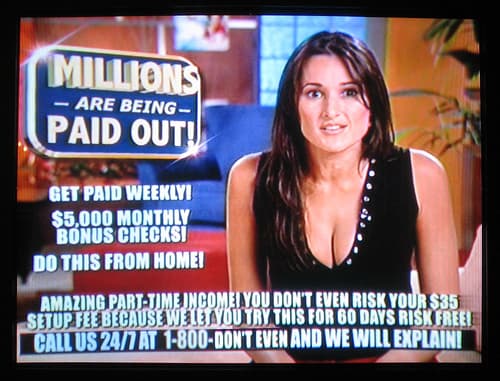
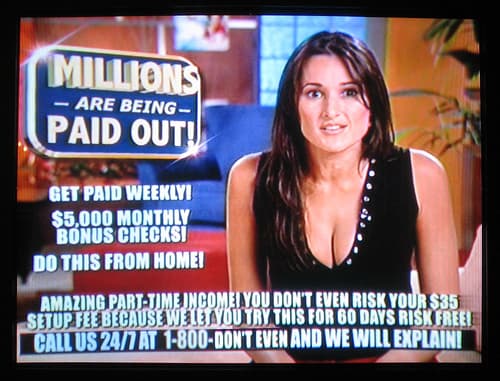
Nov 23, 2019 | Blogging, Business, Consumer, Employees, Employment, Facebook, Google, Hacking, Identity Theft, Imposter Sites, Internet, LinkedIn, Radio Show, Radio_Show, Security, Technology
Hiring and Issues with Scam Online Applications With the economy buzzing along and employment at a full time high — finding workers for seasonal part time employment is getting harder and harder. However, these employers are now having to compete with...

Nov 23, 2019 | Banking, Banking, Big Tech, Big Tech, Business, Cashless, Facebook, Facebook, Financial, Gifts, Internet, Online, Radio Show, Radio_Show, Shopping, Social Networking, Technology
Another “Pay–ment” System Introduced Contactless payment solutions are becoming quite popular and now Facebook will be launching their version, Facebook Pay. Although not used like the current other contactless systems, you will be able to use it on all their...

Nov 23, 2019 | Advertising, Android, Big Tech, Black Friday, Business, Cell Phone, Cyber Monday, Cybercrime, Financial, Gifts, Hackers, Hacking, Hacking, Internet, iPhone, Liability, Online, Passwords, Patching, Phishing, Phone, Phones, Privacy, Radio Show, Radio_Show, Retail, Security, Security Alerts, Shopping, Smart Phone, Technology, Updates
Hand in Hand On Black Friday — Shopping and Privacy Black Friday is almost upon us! The day that retailers finally able to move from a red accounting register on to the black and it is always met with sales and loss leaders (great prices but not for the...
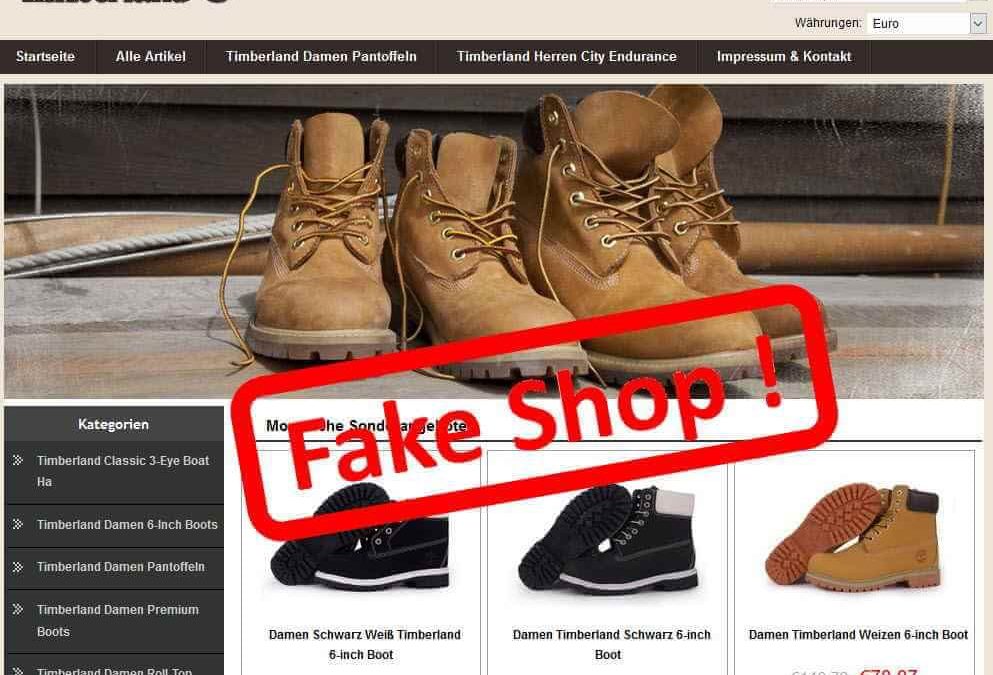
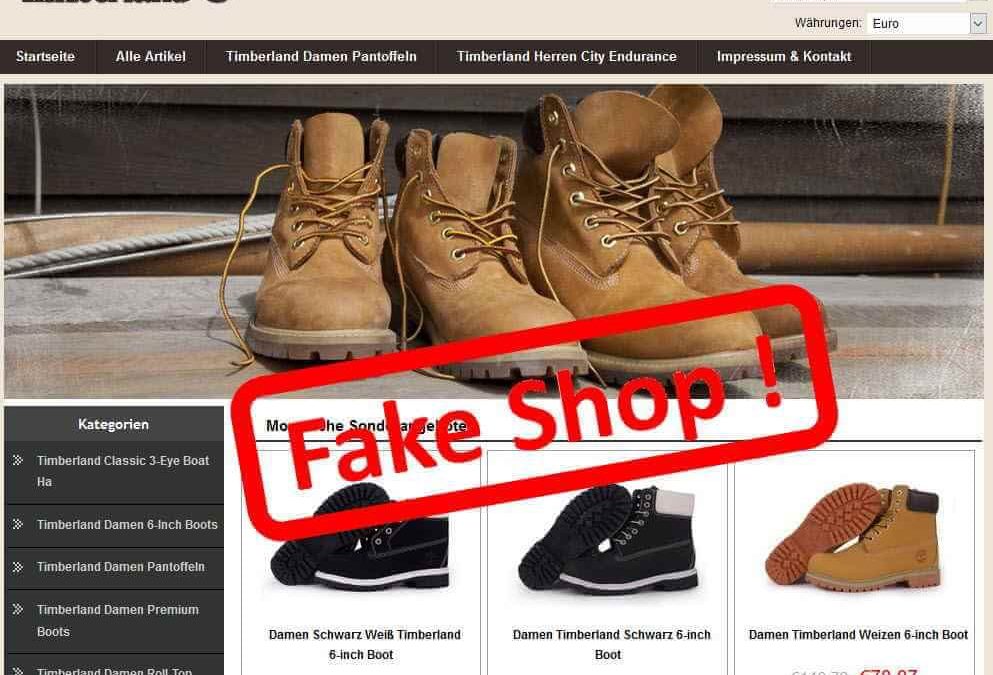
Nov 23, 2019 | Advertising, Black Friday, Business, Consumer, credentials, Cyber Monday, Cybercrime, Family, Gifts, Identity Theft, Imposter Sites, Internet, Online, Patching, Phishing, Phishing, Phones, Radio Show, Radio_Show, Retail, Security, Security Alerts, Updates
Imposter Retailers Outnumber Legitimate Ones Are you ready for the extreme online shopping season! While you can purchase items online anytime, holiday e-commerce sales reached $126 billion last year with Cyber Monday online purchases generating $7.9 billion...

Nov 16, 2019 | Business, Business Email Compromise, CEO, Consumer, credentials, Cyber breaches, Cybercrime, Cybersecurity, DeepFake, Employees, Employment, Exploits, Family, Hackers, Hacking, Hacking, HR, Liability, Phishing, Phishing, Psychology, Radio Show, Radio_Show, Security, Technology
Don’t Take The Bait – Fake Sexual Harassment Claims Scammers are phishing employees of large corporations using fake US EEOC sexual harrassment complaints to offload trojan payloads of Trickbot malware onto corporate computers which direct them to hand over...

Nov 16, 2019 | Best Practices, Business, Business Email Compromise, credential stealing, credentials, Cyber breaches, cyberattacks, Cybercrime, Cybersecurity, CyberTraining, Employees, Employees, Hackers, Hacking, Hacking, Hacking, Liability, Phishing, Phishing, Radio Show, Radio_Show, Security, Security, Technology, third-world
Can You Detect A Phishing Attempt? Cybercriminals are getting better at crafting believable and sophisticated ilephishing emails that are undetectable from legitimate emails. Do you know how to spot them? If you suspect that an email is not legitimate you can...