Dec 19, 2019 | Backup, Business, credential stealing, Cyber Liability, cyberattacks, Cybersecurity, Data Storage, Fines and Penalties, Government, Hacking, Hacking, hacking as a service, Hacks, Incident Response, Insider Threat, Internet, Malware, Networking, Patching, Radio Show, Radio_Show, Regulation, Security, Security Alerts, Software As A Service, Technology, Third - Party, Updates
Are You At Risk from Your Outsourced Software Provider The “Cloud” is the eponymous name given for a computer server that belongs to another person or company that you have no control over. There are many companies who offer computing services to...

Dec 19, 2019 | Applications, Attack Vectors, Business, Business Email Compromise, credential stealing, credentials, Cyber breaches, cyberattacks, Cybercrime, Cybersecurity, Financial, Government, Hackers, Hacking, Hacking, Hacking, hacking as a service, Incident Response, industrial espionage, Insider Threat, Intellectual Property Theft, Internet, Malware, Nationstates, Networking, Operating Systems, Organized Crime, Password Managers, Passwords, Patching, Phishing, Radio Show, Radio_Show, Ransomware, Security, Security Alerts, Software As A Service, Technology, third-world, Updates, Windows (Microsoft)
Lessons We Failed To Learn and Therefore Are Doomed To Repeat It seems as every year gets worse and worse when it comes to Cyber Breaches and Cyberattacks. Compared to 2018 were have had 33% more breaches this year. They are, after all of our data, personally...

Dec 19, 2019 | Anti-Virus, Attack Vectors, Business, Cybersecurity, Firewalls, Internet, Malware, Networking, Radio Show, Radio_Show, Security, Signature-Based, Technology, VPN, Vulnerabilities
Signature Anti-Virus does not adequately protect you from today’s Malware Today’s malware acts much differently and can disguise itself more effectively than previous generations of malware. The designs of most anti-virus do not take that into...

Nov 30, 2019 | Business, Computers, Cyber breaches, cyberattacks, Cybercrime, Data Storage, Employees, Firewalls, Hackers, Hacking, Hacking, Hacking, Insider Threat, Intellectual Property Theft, Internet, Malware, Malware, Networking, Networking, Patching, Privacy, Radio Show, Radio_Show, Routers, Security, Security Alerts, segmentation, Technology, Updates, Vulnerabilities
Why Zero Trust Is the Answer to Internet Everywhere Connections Everyone everywhere has a mobile device, and connections to the internet are available whenever we want it. In our connected world, it means that keeping your businesses secure means fighting a...
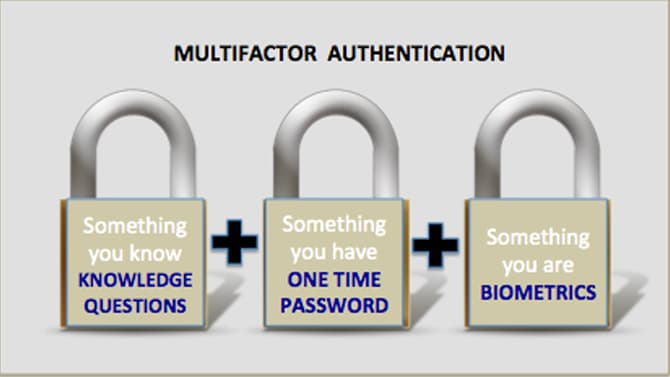
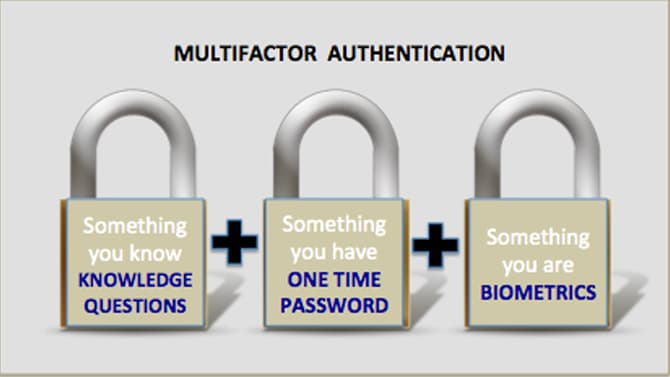
Nov 16, 2019 | 2FA, Best Practices, Business, Computers, credentials, Cyber breaches, cyberattacks, Cybersecurity, Employees, Employees, Hacking, Hacking, hardware token, Internet, Laptops, Malware, MFA, Phishing, Radio Show, Radio_Show, Security, Security, Technology
Best Practices in Authentication Still Mostly Ignored By Businesses How do cybercriminals breach into corporate systems? They use many tactics but on of the easiest is through the use of compromised credentials. The problems is that these are real valid credentials...

Nov 9, 2019 | Applications, Artificial Intelligence, Audit Logs, Best Practices, Business, credentials, Cyber breaches, cyberattacks, Cybercrime, CyberTraining, data sharing, Data Storage, Databases, Employees, Employees, Firewalls, Firewalls, Hackers, Hacking, Hacking, Hacks, Hard Disks, Intellectual Property Theft, Laptops, Liability, Malware, Malware, Networking, Networking, Patching, Radio Show, Radio_Show, Ransomware, Routers, Security, Security, Security Alerts, segmentation, Software As A Service, Switches, Technology, Updates
Cyberbreaches cause Small Businesses to Close Cybercriminals have found a lucrative new target – the small business. Unfortunately, for a tenth of them the breach meant closing their doors forever. The impacts on small businesses is excentuated greatly....