Aug 17, 2019 | Cybercrime, CyberTraining, Employees, Encryption, Financial, Hackers, Hacking, Internet, Malware, Passwords, Radio Show, Radio_Show, scam, Security, Security, Security, Social Networking, Technology
Technology Makes Crime Easier In part one of TechRepublic’s four-part series “Mastermind con-man behind Catch Me If You Can talks cybersecurity” TechRepublic’s Karen Roby sat down with Frank Abagnale, the famous con man turned FBI...
Aug 10, 2019 | Best Practices, Business, Cloud Vendors, Computers, Cryptocurrency, Cyber breaches, Cybercrime, Financial, Hackers, Hacking, Hacking, Internet, IoT, Liability, Malware, Nationstates, North Korea, Radio Show, Radio_Show, Ransomware, Ransomware, scam, Security, Security, Technology
North Korea. What do you think when you hear about this country? You probably think of a nation that has separated from progress and technology. A country run by a socialist despot. A hermit kingdom that strictly controls the daily activities of its people. A country...

Aug 10, 2019 | automation, Best Practices, Breaches, Business, Cybercrime, Cybersecurity, Data, Data Storage, Databases, Equifax, Hacking, News, Privacy, Radio Show, Radio_Show, Security, Security, settlement
Did You Get Your Equifax Settlement? Settlement Drained in a WeekSo many people have made claims in the data-breach settlement against consumer credit rating agency Equifax that, according to the Federal Trade Commission, each claimant is now likely to get...
Aug 3, 2019 | Business, Cybersecurity, Employees, Employees, Radio Show, Radio_Show, Security
Retain Employees Increase Security People, processes, and technology: the three most important components of security operations. Processes can be designed and documented, technology can be purchased and implemented, but people are most often the X...
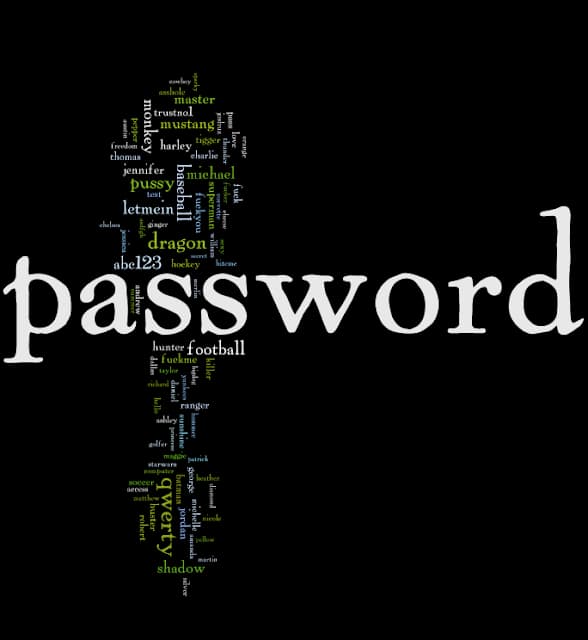
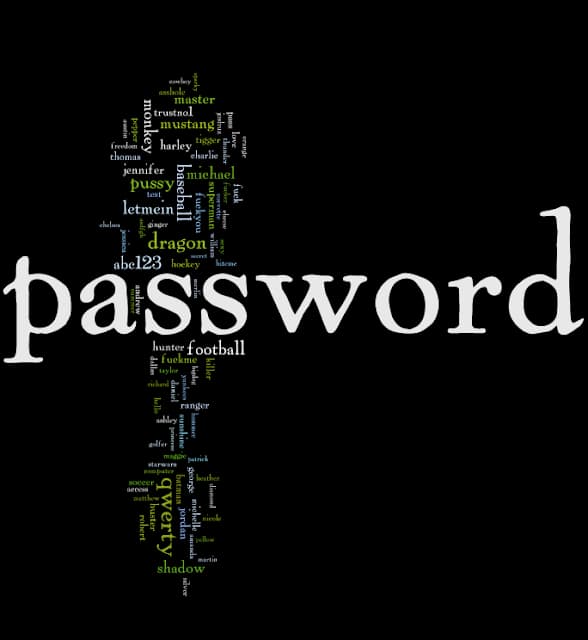
Aug 3, 2019 | Best Practices, Business, Cybercrime, Data Storage, Hacking, Hacking, Passwords, Privacy, Radio Show, Radio_Show, Security, Security, storage, Technology
Storing your Password in Plaintext…Say What???? Stock trading company Robinhood has admitted to storing passwords of some of its users in plaintext. The California-based firm said that it came across this security lapse on Monday this week. In an email,...

Aug 3, 2019 | Best Practices, Business, CEO, Cloud Vendors, Computers, CyberTraining, Legal, Radio Show, Radio_Show, Regulatory Compliance, Security, Security, Security Assessments
SMB Cyber Security and Audits. The Why’s, the How’s, and the steps… Why? To maintain your company’s “security hygiene.” To identify critical weaknesses in your cybersecurity protection measures To Keep in Compliance with Industry...