Nov 9, 2019 | Android, Android, Applications, Applications, applications, Biography, Business, Cars, Coding, Consumer, Hacking, Hacking, Hacks, Internet, iOS, iPhone, Mapping, Mobile, Mobile Phones, Navigation, Patches, Patching, Phone, Phones, Radio Show, Radio_Show, safety, Security, Security Alerts, Smart Phone, Software Manufacturers, Technology, Third-Party, Tracking, Travel, Updates, vehicles
Powerful Apps allow Control for…. Ever! Many companies are creating apps and they are powerful. They are convenient and offer ease of use to their product lines. However, they may not have concidered the implications when not used in the manner that they...
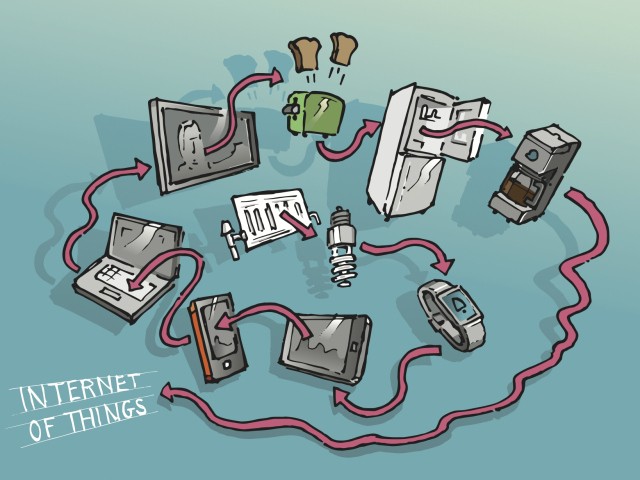
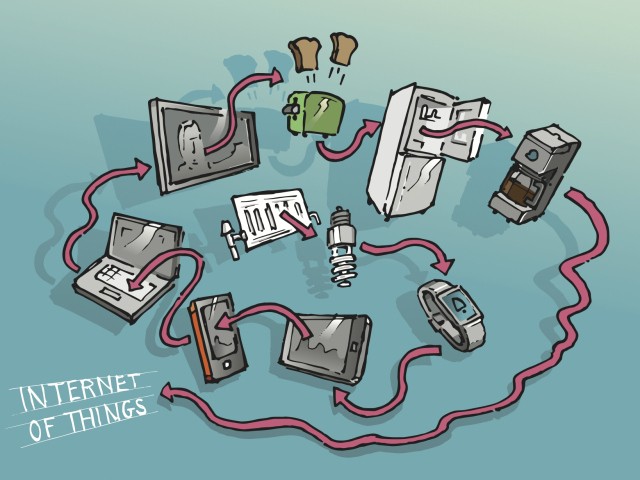
Nov 9, 2019 | Applications, Best Practices, Business, gadgets, Hacks, Infosec, Internet, IoT, Liability, Networking, Patches, Patching, Radio Show, Radio_Show, Security, Security, Security Alerts, segmentation, Software, Technology, Third-Party, Updates, Updates
Oops —- We Designed Technology to be Unpatchable IoT or Internet of Things devices are becoming more and more popular. It seems that all types of items we never considered to require connectivity are now connected to the internet. They are constantly passing...

Oct 19, 2019 | automation, bluetooth, Business, Consumer, cyberattacks, Cybercrime, gadgets, Hackers, Hacking, Hacking, Hacking, Hacks, Infosec, Intellectual Property Theft, Internet, IoT, Monitoring, Nationstates, Organized Crime, Passwords, Patching, Radio Show, Radio_Show, Security, Security, Security Alerts, Smart Home, spying, Surveillance, Technology, Updates
Convenience Gadgets – Design, Functionality then Security The first half of this year has been marked with a rampant increase on all those little gadget devices known by the acronym, IoT. These are any small device or controller that is network connected....

Oct 12, 2019 | Best Practices, Business, Cyber breaches, cyberattacks, Cybercrime, Cybersecurity, Hackers, Hacking, Hacks, industrial espionage, Internet, Malware, Radio Show, Radio_Show, Security, Security, Technology
More Than Three-Quarters of US Businesses Are CyberAtttack Targets Cybersecurity incidents are up! Hackers worldwide favorite target du jour are U.S. small and medium-sized businesses. Unfortunately, for many, they have fallen back on the false idea they are...

Oct 5, 2019 | Business, Civilian Employment, Contractors, Cybersecurity Professional, Employment, IT Professional, Jobs, Military, Radio Show, Radio_Show, Technology, Under Arrest
Terminated Government Contractor Ends Up in Jail After Destroying IT System Resources IT people are hard to come by and are getting harder to find. That goes for business and government alike. In late 2016 the government terminated a contract with an IT Systems...

Sep 14, 2019 | Best Practices, Cyber breaches, cyberattacks, Cybercrime, Cybersecurity, Hackers, Hacking, Hacks, Legal, Radio Show, Radio_Show, Security, Security, Technology
Successful Cybercriminals Require Your Help Most cybercriminals target people, not infrastructure: More than 99% of emails distributing malware from 2018 into 2019 required human interaction to click links, open documents, accept security warnings, or complete other...