The Latest in Tech Today
Did your Brain suffer from those puffs of that High School Cigarette?
Did your Brain suffer from those puffs of that High School Cigarette? After decades of educational programming and advertising, regular cigarette smoking and sales in the United States have declined to their lowest levels in 50 years. But doctors and parents...
Millions at Risk from Flaw in BitDefender’s Free Anti-Virus
Millions at Risk from Flaw in Microsoft’s Free Anti-Virus These days, there's not a week that goes by without news of some serious security breaches, and this month was no different despite the summer break—we can thank in part the BlackHat and DefCon...
Unsecured IoT is a Playground for Hackers
Unsecured IoT is a Playground for Hackers Playground Microsoft made news recently at the annual Black Hat conference in Las Vegas, generating a lot of buzz about its discovery of a malicious Russian hacker group using some common Internet of Things (IoT)...
Surprising way you may die on your next trip to the hospital. Another huge cyber security risk.
Security First Mindset evades Medical Devices leaving them Vulnerable
Security First Mindset evades Medical Devices leaving them Vulnerable "Everything with a powerpoint is probably connected, or will be shortly," says Christopher Neal, chief information security officer (CISO) of Ramsay Health Care. "Increasingly that...
What is More Destructive a Nuclear Weapon or Cyber Attack
What is More Destructive a Nuclear Weapon or Cyber Attack People around the world may be worried about nuclear tensions rising, but I think they’re missing the fact that a major cyberattack could be just as damaging – and hackers are already laying the...
Missing Updates on Applications Creates Vulnerabilities
Missing Updates on Applications Creates Vulnerabilities Avast’s PC Trends Report 2019 found that users are making themselves vulnerable by not implementing security patches and keeping outdated versions of popular applications on their PCs. The applications...
Your Login Credentials are Keys to the Kingdom for Hackers
Your Login Credentials are Keys to the Kingdom for Hackers A recent study published by Google estimates that 1.5% of all login credentials used across the web have been compromised in data breaches and are vulnerable to credential stuffing attacks. Google has...
You Can Change Your Password but You Can’t Change Your Fingerprints
You Can Change Your Password but You Can’t Change Your Fingerprints The biggest known biometric data breach to date was reported recently when researchers managed to access a 23-gigabyte database of more than 27.8m records including fingerprint and facial...
Employee Privacy vs Network Security: The Matchup
Employee Privacy vs Network Security: The Matchup PRACTICALLY all governments and industry regulators now demand that companies secure their enterprise networks to protect their systems and data. In responses, companies are doing everything in their capacity to...
Live in Sweden Save Your Cash and Coin
Live in Sweden Save Your Cash and Coin For years, we have commented on the Swedish government and the Riksbank pushing for a “cashless society.” The Riksbank has over 1,000 articles posted on its website on the “cashless society“. The emphasis worked: between...
Facebook News takes Another Hard Left Turn
Facebook News takes Another Hard Left Turn Facebook confirmed on Tuesday it’s hiring a team of veteran journalists to help curate stories in its soon-to-launch news tab. The company confirmed the plans after The New York Times reported that Facebook is...
Ransomware Attacks Strike 20% of Americans
Ransomware Attacks Strike 20% of Americans Cybercriminals have been using ransomware to profit off of unprepared victims for more than a decade. Ransomware rose to infamy when the WannaCry and NotPetya attacks struck the world. Recently, attackers have...
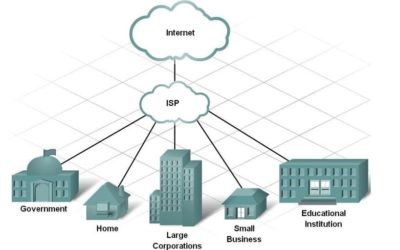
IoT – Putting our Business Networks and Security at Risk
IoT - Putting our Business Networks and Security at Risk IoT - Putting our Networks and Security at Risk Just take a look at any website or catalog, and you will see the availability of hundreds to thousands of connected devices touted to make your life...
Turns Out It Wasn’t Just Capital One
Turns Out It Wasn’t Just Capital One Federal prosecutors say a woman charged in a massive data breach at Capital One may have hacked more than 30 other organizations. Paige Thompson, of Seattle, was arrested last month after the FBI said she obtained personal...
Phishing — Best Practices
Phishing — Best Practices One of the most persistent security challenges is phishing. This is true for both organizations and individuals. Whether gaining access to credit card information, security passwords, or any other sensitive information, hackers can use...
Want To Be A Security Pro —- Tips Here!
Want To Be A Security Pro —- Tips Here! As cyber criminals grow more sophisticated and news of major breaches reach headlines nearly daily, cybersecurity professionals are in high demand: There are currently nearly 3 million unfilled cybersecurity jobs...
Your Cyber Insurance Policy Probably Won’t Pay Out
Your Cyber Insurance Policy Probably Won’t Pay Out More businesses are recognizing the need for cyber insurance as part of an overall security strategy. Here are some key points to consider when evaluating, purchasing, and relying on a policy. After years of...
Technology Makes Crime Easier
Technology Makes Crime Easier In part one of TechRepublic's four-part series "Mastermind con-man behind Catch Me If You Can talks cybersecurity" TechRepublic's Karen Roby sat down with Frank Abagnale, the famous con man turned FBI Academy instructor, who...
Microsoft is Dragging It’s Feet on Another Security Vulnerability
Microsoft is Dragging Its Feet on Another Security Vulnerability On Tuesday, Tavis Ormandy of Google's Project Zero released an exploit kit called ctftool, which uses and abuses Microsoft's Text Services Framework in ways that can effectively get anyone...
So Far its Only AT&T and T-Mobile Doing Something About Spam Phone Calls
So Far its Only AT&T and T-Mobile Doing Something About Spam Phone Calls AT&T and T-Mobile announced a joint anti-robocall initiative today, but they didn't promise any new call-blocking capabilities for their customers. The carriers made a big deal of...
Huge Valuation’s Lead to Huge Losses…Again.
Huge Valuation’s Lead to Huge Losses…Again. A ghost of unicorns past ominously re-surfaced yesterday evening. Verizon agreed to sell its blogging website Tumblr to Automattic, the owner of WordPress.com, for less than $3 million, according to Axios. It’s crazy...
Another Reason to Check Those Daily Deliveries
Another Reason to Check Those Daily Deliveries Penetration testers have long gone to great lengths to demonstrate the potential chinks in their clients' networks before less friendly attackers exploit them. But in recent tests by IBM's X-Force Red, the...
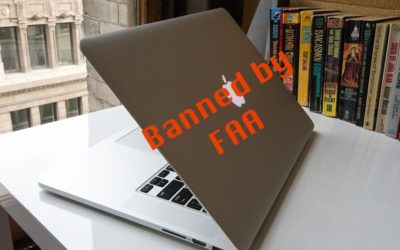
MacBooks Get Grounded — for Good Reason
MacBooks Get Grounded — for Good Reason The Federal Aviation Administration has banned certain 15-inch MacBook Pros with potentially defective batteries from US flights. The move, which follows Apple's June recall announcement, is part of a general FAA policy...
Am I Going Crazy or Did Elizabeth Warren actually Make Sense for Once
Am I Going Crazy or Did Elizabeth Warren actually Make sense for Once Equifax's massive 2017 data breach screwed over more than 140 million people, so it was not terribly surprising when tens of millions of people jumped at the opportunity to claim cash money...
My Opinion about VPNs – Answering a question from a listener
[Because I had this question from a listener about VPNs this week, and since it's such a hot topic, I thought I'd forward the email thread to you (with Dave's permission). I go into when you need to use a VPN, what you need to be aware of, and some more insider tips...
A Nation of Super Hackers and They are Coming For Your Business!
North Korea. What do you think when you hear about this country? You probably think of a nation that has separated from progress and technology. A country run by a socialist despot. A hermit kingdom that strictly controls the daily activities of its people. A...
Poor Performing ISP Looses Customers
On the 10th anniversary of the App store, it’s time to delete most of your apps Poor Performing ISP Loses Customers Frontier Communications yesterday reported lower revenue and a $5.45 billion goodwill impairment charge, and it warned investors that its revenue...
Everybody has A Price — AT&T Learned Their Employees
Everybody Has A Price -- AT&T Learned Their Employees AT&T employees took bribes to unlock millions of smartphones and to install malware and unauthorized hardware on the company's network, the Department of Justice said yesterday. These details come...
Old Scam on Uptick – Beware
Old Scam on Uptick - Beware A long-running scam email campaign that pretends to be an unsubscribe confirmation request has seen an uptick recently. These emails should never be clicked on or responded to as they are designed to harvest working email addresses...