Jan 18, 2020 | Access Controls, Applications, Attack Vectors, automation, Business, CEO, Coding, Compliance, credential stealing, Cyber breaches, Cyber Liability, cyberattacks, Cybercrime, Cybersecurity, Data Storage, Hackers, Hacking, Hacking, Internet, Patching, Radio Show, Radio_Show, safety, Security, Security Alerts, spying, Technology, Third - Party, Updates
A Lesson to Learn – If it is Connected It can Be Hacked I remember years ago at CES 2013, when this young entrepreneur scheduled an interview with me to show off a prototype for his new Ring security device. At the time, IoT was in its infancy, and this product...
Jan 19, 2019 | Radio Show, Security
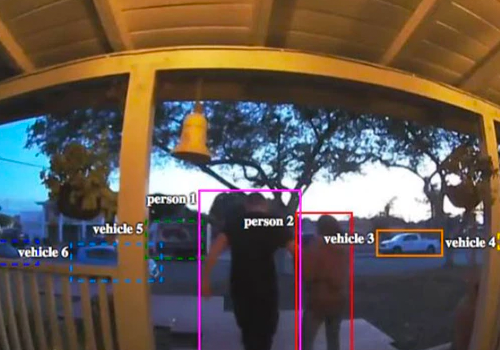
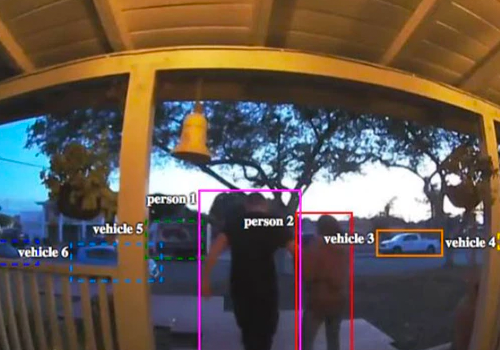
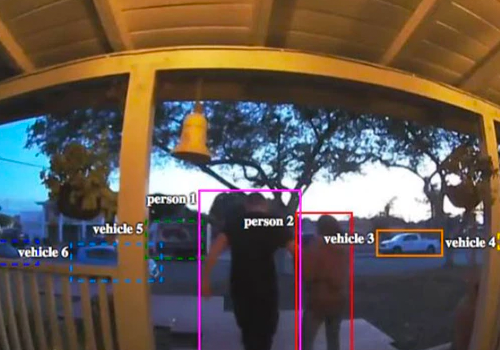
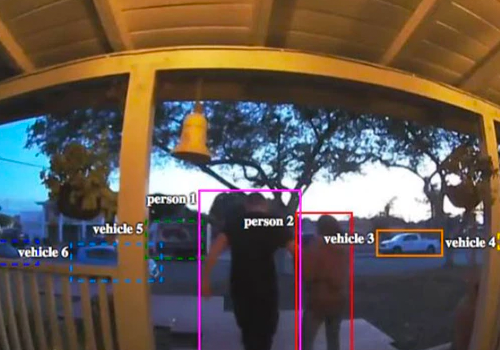
For Owners Of Amazon’s Ring Security Cameras, Strangers May Have Been Watching Too THE “SMART HOME” of the 21st century isn’t just supposed to be a monument to convenience, we’re told, but also to protection, a Tony Stark-like bubble of vigilant algorithms and...