Feb 19, 2021 | Access Controls, Apple, Applications, Apps, Artificial Intelligence, Attack Vectors, Authentication, Big Tech, Bitcoin, Breaches, Business, Credentials, Cryptocurrency, Cryptocurrency, Cryptomining, Cyber breaches, cyberattacks, Cybercrime, Cybersecurity, Employees, Financial, Firewalls, Google, Google, Google Play Store, Government, Hackers, Hacking, Human Element, Infrastructure, Internet, Legacy Systems, Malware, Malware, Microsoft, Microsoft, Monitoring, NASA, Networking, News, Patches, Podcast, President Joe Biden, Radio Show, Radio_Show, Regulatory Frameworks, Security, Security Alerts, Show Notes, Software, Technology, Technology, trojans, updates and patches, Utilities, Vulnerabilities, Windows (Microsoft), Zero Trust
Read. Learn. Share Tech Talk Show Notes February 20. 2021 Breached water plant employees used the same TeamViewer password and no firewall The Florida water treatment facility whose computer system experienced a potentially hazardous computer breach last week used an...

Oct 5, 2019 | Advertising, Android, Android, Exploits, Google, Google, Hacking, iPad, Malware, Mobile, Organized Crime, Radio Show, Radio_Show, Smart Phone, Software Manufacturers, Tablet, Technology, Tracking
Google Play “Malware” Store — Poor App Management Platform If you want to download apps for your smartphone or tablet, there are many choices. However, the two primary sources are the App Store, for Apple devices and the Google Play Store, also known as the...
Jun 29, 2019 | Advertising, Breaches, cell phones, Cybersecurity, Hacking, iPad, Malware, Phones, Privacy, Radio Show, Radio_Show, Security, Security, Smart Phone, Software, Software Manufacturers, Tablet, Technology, Tracking
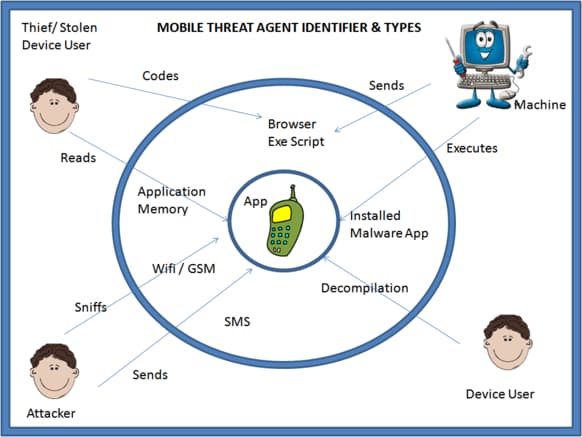
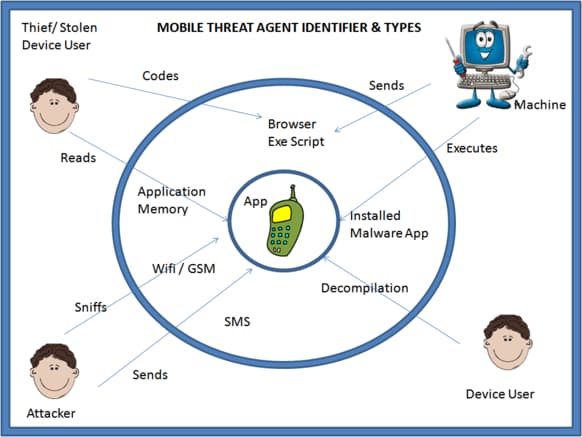
Is That App On Your SmartPhone Safe? Maybe Not! High-risk vulnerabilities are common across both Android and iOS mobile apps, with Android devices slightly more at risk than their iOS counterparts (43% vs. 38%), according to Positive Technologies’...