Feb 1, 2020 | Access Controls, Anti-Virus, Applications, Attack Vectors, Audit Logs, Best Practices, Business, cyberattacks, Cybercrime, Cybersecurity, Data Assets, Disaster_Preparedness, Hackers, Hacking, Hacking, Incident Response, Legacy Systems, Liability, Malware, Monitoring, Operating Systems, Patching, Radio Show, Radio_Show, Security, Security, Security Alerts, Technology, Updates, Zero-Day
Keeping Legacy Software Safe The primary problem with legacy software is keeping it secure. Many businesses are using software that was developed years ago and before many of these new attack variants were ever even considered. That means that they were not designed...
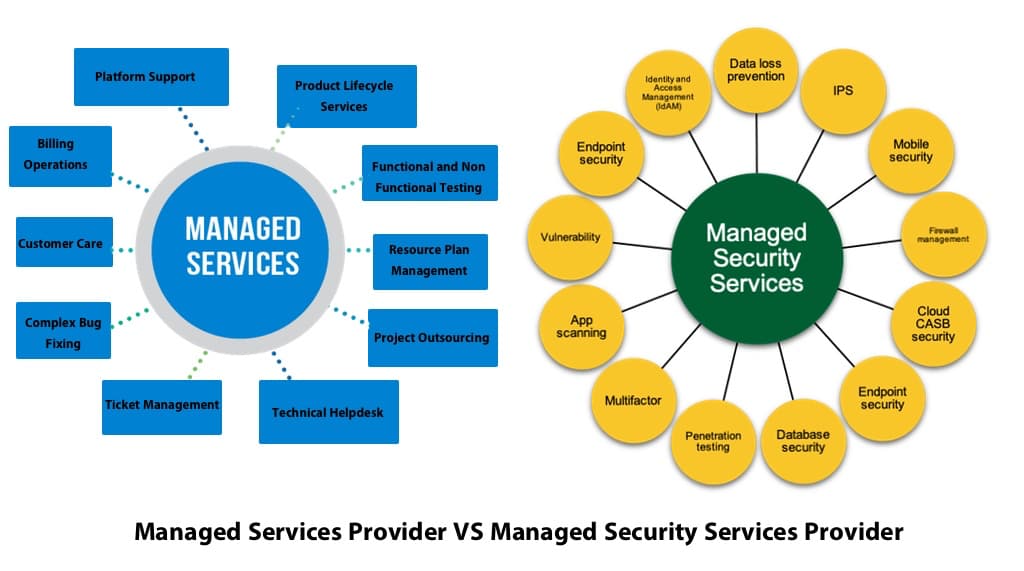
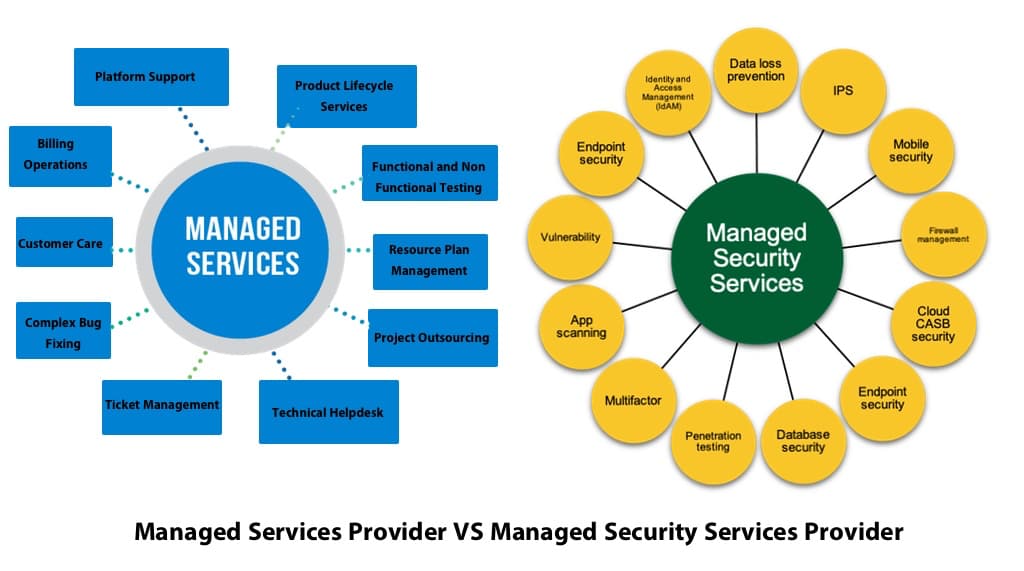
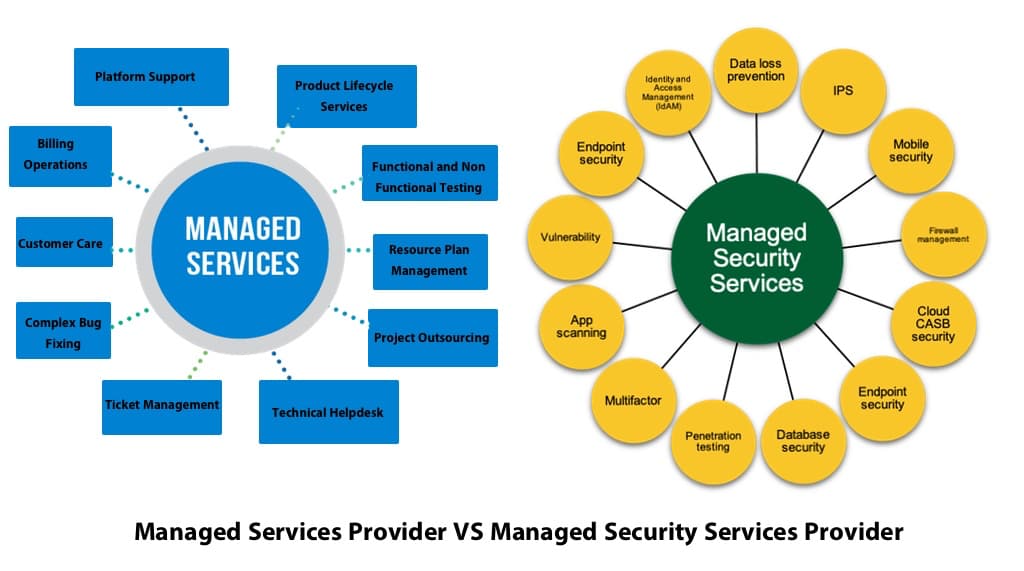
Nov 23, 2019 | Business, Computer Repair, Computers, Disaster_Preparedness, Employment, Facebook, Google, Internet, Internet Service Providers, LinkedIn, Managed Security Services Provider (MSSP), Managed Services Provider (MSP), Networking, Operating Systems, Privacy, Radio Show, Radio_Show, Remote Repair, Security, Technology
The hanging of an MSP “Shingle” and Your Business Security Are you in the cross hairs of hackers? How can a hacker multiply his efforts? By attacking a company who protects other companies. Hackers new targets are the Managed Services providers (MSPs) because...