Aug 17, 2019 | Best Practices, Business, Cybercrime, CyberTraining, Employees, Employees, Hackers, Hacking, Hacking, Liability, Malware, Malware, Passwords, Phishing, Privacy, Radio Show, Radio_Show, Ransomware, Regulatory Compliance, scam, Security, Security, Technology
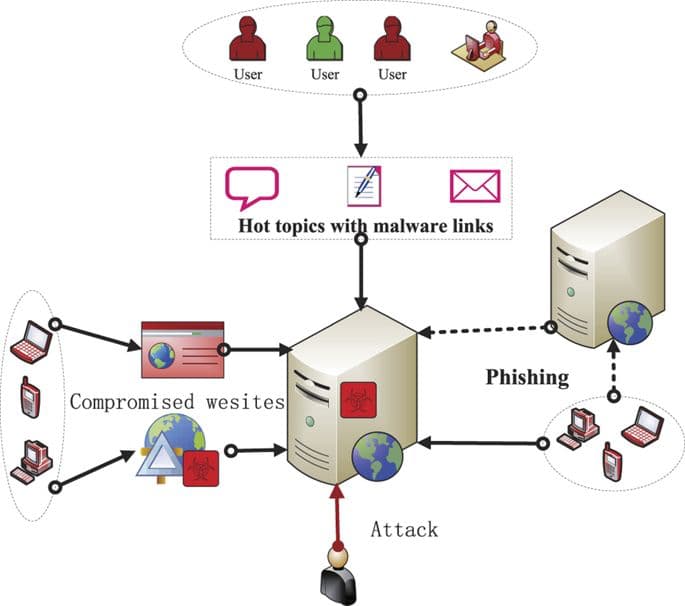
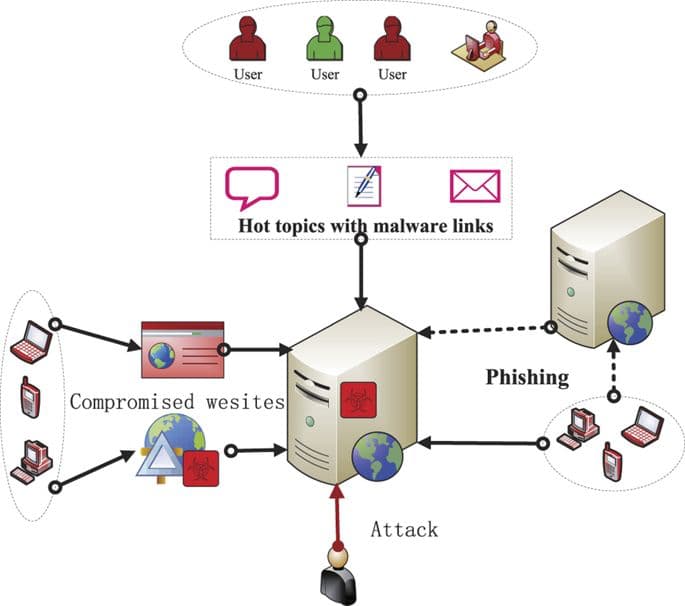
Phishing — Best Practices One of the most persistent security challenges is phishing. This is true for both organizations and individuals. Whether gaining access to credit card information, security passwords, or any other sensitive information, hackers can use...

Aug 17, 2019 | Business, Computers, Cybersecurity, Malware, Microsoft, Microsoft, Radio Show, Radio_Show, Software Manufacturers, Technology, Windows (Microsoft)
Microsoft is Dragging Its Feet on Another Security Vulnerability On Tuesday, Tavis Ormandy of Google’s Project Zero released an exploit kit called ctftool, which uses and abuses Microsoft’s Text Services Framework in ways that can effectively get...
Jul 6, 2019 | Business, Computers, Cybercrime, Malware, Malware, Organized Crime, Radio Show, Radio_Show, Ransomware
Organized crimes latest drive-by’s attacking website visitors An ongoing operation that’s installing ransomware and other malware on the computers of unsuspecting website visitors is one of the most potent drive-by attack campaigns researchers have seen in...

Jun 29, 2019 | automation, Computers, Cybersecurity, Hacking, Intel, Malware, Microsoft, Military, Radio Show, Radio_Show, Security, Surveillance, Technology, Warfare
Trumping Iranian Aggression The US has responded to a recent rise in Iranian cyber-activity and the shooting of an unarmed drone last week by launching cyber-attacks against Iran’s military IT systems. The cyber-attacks were carried out by US Cyber...

Jun 29, 2019 | Computers, Cybersecurity, iPad, Malware, Malware, Radio Show, Radio_Show, Technology
Mac Non-Vulnerability Vulnerability Mac malware developers have jumped on a recently disclosed macOS Gatekeeper vulnerability and are actively developing malware that abuses it. The new malware has been named OSX/Linker and has been tied to the same group that...
Jun 29, 2019 | Business, Cloud, Computers, Cybersecurity, data sharing, Malware, Privacy, Radio Show, Radio_Show, Security, Security, Technology
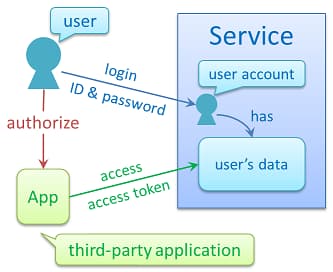
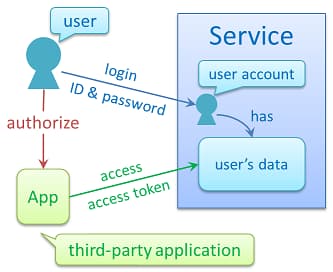
Who Is Your Biggest Cyber Liability? Maybe It Is Not Who You Think. If a poll were taken and the top threats to our national and cybersecurity were voted on, the usual suspects would be easy to name: China, Russia, North Korea, and Iran. You’d be half right....