Nov 9, 2019 | anonymity, Applications, Audit Logs, audit logs, automation, Big Tech, Business, Cloud Vendors, Code-Breaking, Computers, Consumer, credentials, Cyber breaches, Data, Data Storage, Databases, Elections, Elections, Encryption, Government, Hackers, Hacking, Hard Disks, Internet, Legal, Machine Learning, Malware, Nationstates, Networking, Online Voting, Organized Crime, Patching, Radio Show, Radio_Show, Security, Security Alerts, Software As A Service, Technology, Updates, Voting Technology
Online Voting is a Disaster waiting to Happen If it is connected it can be hacked. The risk of only digital data that can not be audited is just a sure way to assure meddling and hacking of our elections. The integrity of our elections must remain paramount if...
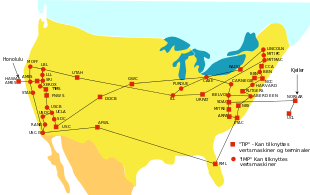
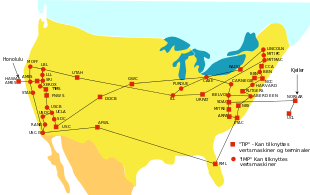
Nov 9, 2019 | ARPA, Business, Computers, Data, data sharing, Future Workforce, Government, Internet, Legacy, Military, Multitasking, Networking, Networking, Open Source, Projects, Radio Show, Radio_Show, Technology, Utilities
Technology idea that started 50 years ago but we rely on today It has taken 50 years to bring the network we know today as the internet to this point. In October 1969 the Advanced Research Projects Agency designed a network that research investigators could...

Oct 12, 2019 | Business, Consumer, Cybercrime, Encryption, Government, Hackers, Hacking, Home, Malware, Nationstates, Networking, Networking, NSA, NSA, Organized Crime, Radio Show, Radio_Show, Security, Technology, VPN, VPN
Popular VPNs Are Vulnerable To Exploit Out of all the topics that my listeners inquire about, none is more prevalent than VPNs and VPN security. Unlike what the advertisements seem to indicate (like Norton VPN advertisements you’ve heard on the radio), a VPN is...

Sep 21, 2019 | bluetooth, Business, Cybercrime, Cybersecurity, Hackers, Networking, Networking, Privacy, Radio Show, Radio_Show, Routers, Technology, WiFi
Perils of Public WiFi and How To Protecting Your Information With the abundance of available public WiFi networks that are prompting us to connect whenever we sit down in a public area. Who pays for those WiFi routers, is it a profit point for the business by selling...

Sep 14, 2019 | Business, Cyber breaches, cyberattacks, Cybercrime, Cybersecurity, Electricity, Firewalls, Firewalls, Hackers, Hacking, Hacking, Networking, Patches, Power Grid, Radio Show, Radio_Show, Security, Security Alerts, Software, Technology, Updates, Utilities
Unpatched Firewalls leave US Power Grid Vulnerable to Cyberattacks A cyber-security incident that impacted a US power grid entity earlier this year was not as dangerous as initially thought, the North American Electric Reliability Corporation (NERC) said last week. In...

Sep 14, 2019 | 5G, Android, Android, Best Practices, Cell Phone, cell phones, Cellular Services, Consumer, Cybersecurity, Data, Internet, iOS, IoT, iPhone, Legal, Mobile, Mobile Phones, Networking, Phone, Radio Show, Radio_Show, Security, Security, Smart Phone, Surveillance, Technology, WiFi
Security Demands Up With 5G Zhou Hongyi, co-founder of Chinese internet security provider Qihoo 360 Technology, expects the rollout of 5G mobile services and expansion of the industrial internet to open up more opportunities for the company in the world’s second...