Jan 18, 2020 | Anti-Virus, Applications, Applications, Attack Vectors, Audit Logs, Backup, Best Practices, browsers, Business, Business Email Compromise, Compliance, credential stealing, Cyber breaches, Cyber Liability, cyberattacks, Cybercrime, Cybersecurity, Data, Data Assets, Data Storage, Email, Employees, Employees, Fines and Penalties, Firefox, Government, Hackers, Hacking, Hacking, Hacking, Intellectual Property Theft, Internet, Legacy, Legacy Systems, Liability, Malware, Malware, Nationstates, Networking, Passwords, Patches, Patching, Phishing, Privacy, Radio Show, Radio_Show, Ransomware, Ransomware Attack, safety, Security, Security, Security Alerts, Signature-Based, Software, Technology, Third - Party, Updates, Updates, VPN, Vulnerabilities, Zero-Day
Updates, Patches and Hackers Oh My! Most data breaches ard due to hackers exploiting known vulnerabilities. I know, I hear it all the time – patching takes time, and it can indeed be risky, especially if you have any legacy hardware or software in your network...
Jan 11, 2020 | Anti-Virus, Applications, Attack Vectors, Best Practices, Business, Computers, Cybercrime, Cybersecurity, Data, Hackers, Hacking, Incident Response, Internet, Legacy, Legacy Systems, Malware, Passwords, Patches, Policies and Procedures, Radio Show, Radio_Show, Regulatory Compliance, Regulatory Compliance, Security, Security, Security Assessments, Software, Technology, Updates, Vulnerabilities, Zero-Day
Hackers Preying on Old and Decrepit Technology 1042-02 Cybercriminals will innovate when necessary. However, more likely, like any successful enterprise, they will harvest any low-hanging fruit when and wherever they can find it. For those of us with unpatched older...
Nov 9, 2019 | ARPA, Business, Computers, Data, data sharing, Future Workforce, Government, Internet, Legacy, Military, Multitasking, Networking, Networking, Open Source, Projects, Radio Show, Radio_Show, Technology, Utilities
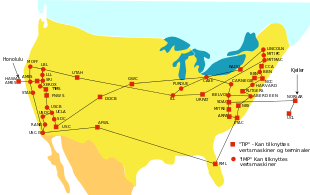
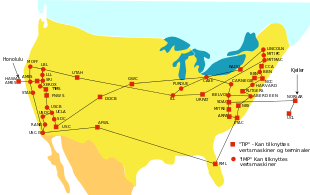
Technology idea that started 50 years ago but we rely on today It has taken 50 years to bring the network we know today as the internet to this point. In October 1969 the Advanced Research Projects Agency designed a network that research investigators could...

Jul 27, 2019 | browsers, Business, Legacy, Radio Show, Radio_Show, Technology
How Old is Your Tech? Certain Boomer basements are little shrines to obsolescence, untidy stockrooms of the one-time cutting-edge: VCRs, corded telephones, immense beige PC monitors, etc. Way fewer Millennials will have basements to store trash in (‘home...