Feb 23, 2023 | Authentication, Best Practices, Business, credentials, Credentials, Cyber Security, Cybersecurity, Hacking, ID Theft, Microsoft, Microsoft, Password Managers, Passwords, Passwords, Privacy, Security, Security, stolen identity, Technology, Threats, Windows (Microsoft)
Locking down your files with a strong password is like putting a virtual lock on your front door. It helps protect your personal or sensitive information from prying eyes, cyber-attacks, or theft. Whether you’re sharing your computer with others or working in a...

May 9, 2020 | Biological Viruses, Business, Coronavirus, Covid-19, Covid-19, Cyber breaches, Cybercrime, Hackers, Hacking, Hacks, Internet, Pandemic, Quarantine, Radio Show, Radio_Show, Security, Technology
Pandemic Hackers are Active – Be Aware Con artists, hackers, cybercriminals will use any excuse to create a plan for defrauding unsuspecting people. COVID-19 is no different, and it has created a swarm of scams related around this pandemic. It is time to open...
Feb 29, 2020 | 2FA, Best Practices, credentials, Password Managers, Passwords, Privacy, Radio Show, Radio_Show, Security, Security, Social Influencers, Technology
Passwords: Length trumps Complexity Complex passwords that must be changed every 90 days are the bain of most companies and a headache for employees and they are not as secure as you have been led to believe. The reason is that people have to write them down. They...

Dec 19, 2019 | Business, Chrome Browser, credentials, Google, Internet, Passwords, Radio Show, Radio_Show, Security, Security Alerts, Technology, Updates
Chrome 79 will continuously scan your passwords against public data breaches Best practices dictate that you should use a different password for every website, application, or program. However, many do not do this, and it is why cybercriminals can run rampant...
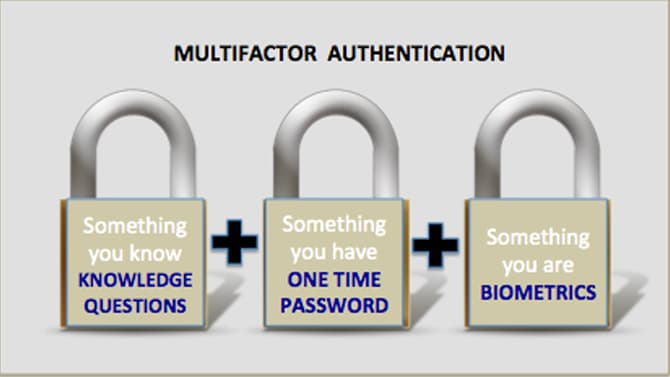
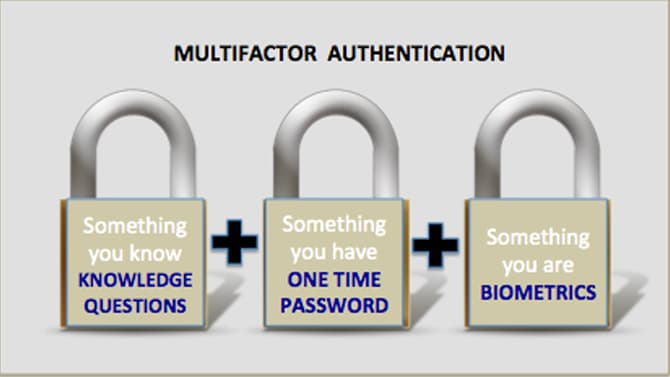
Nov 16, 2019 | 2FA, Best Practices, Business, Computers, credentials, Cyber breaches, cyberattacks, Cybersecurity, Employees, Employees, Hacking, Hacking, hardware token, Internet, Laptops, Malware, MFA, Phishing, Radio Show, Radio_Show, Security, Security, Technology
Best Practices in Authentication Still Mostly Ignored By Businesses How do cybercriminals breach into corporate systems? They use many tactics but on of the easiest is through the use of compromised credentials. The problems is that these are real valid credentials...