Aug 10, 2019 | automation, Best Practices, Breaches, Business, Cybercrime, Cybersecurity, Data, Data Storage, Databases, Equifax, Hacking, News, Privacy, Radio Show, Radio_Show, Security, Security, settlement
Did You Get Your Equifax Settlement? Settlement Drained in a WeekSo many people have made claims in the data-breach settlement against consumer credit rating agency Equifax that, according to the Federal Trade Commission, each claimant is now likely to get...
Aug 3, 2019 | Business, Cybersecurity, Employees, Employees, Radio Show, Radio_Show, Security
Retain Employees Increase Security People, processes, and technology: the three most important components of security operations. Processes can be designed and documented, technology can be purchased and implemented, but people are most often the X...
Aug 3, 2019 | Cybercrime, Cybersecurity, Hackers, Radio Show, Radio_Show, Ransomware, Security
Cybercrime costs are Rising The costs of cybercrime are extremely high these days. This year we’ve seen how a church lost $1.75 million in a BEC scam; two cities in Florida paid ransoms totaling over a million dollars after ransomware attacks; and British Airways had...

Jul 27, 2019 | Breaches, Computers, Consumer, Cyber breaches, Cybercrime, Cybersecurity, Hacking, Laptops, Malware, Radio Show, Radio_Show, Security, Security, Surveillance, Technology, Tracking, Video, Windows (Microsoft)
Is Someone Lurking in Your Computer? Whether you’re in an open office where colleagues regularly wander past or live somewhere—like a college dorm—where you may feel comfortable leaving your laptop unattended in the presence of relative strangers, it can be all...
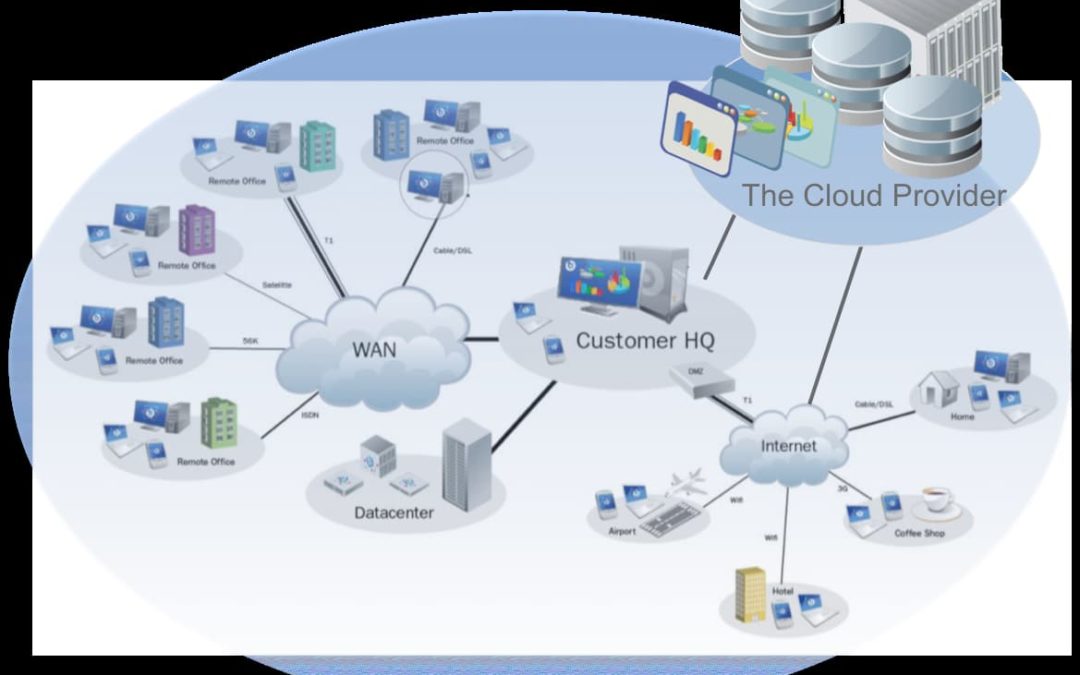
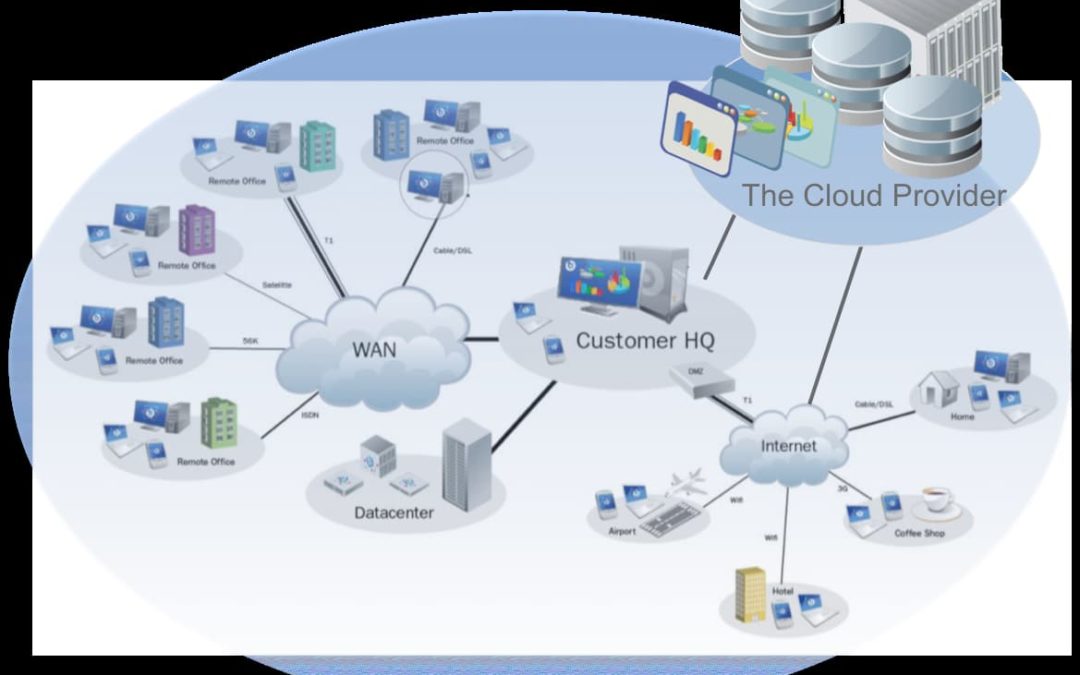
Jul 27, 2019 | Best Practices, Business, Cloud, Cloud Vendors, Computers, Cybersecurity, Internet Service Providers, Networking, Radio Show, Radio_Show, Security, Security, Technology
Are Your Cloud Vendors Paying Attention to Security? Cloud adoption is on the rise: According to International Data Corporation (IDC)’s “Nine Ways to Maximize the Value of Cloud Contracts,” 52 percent of all companies are currently using cloud-based delivery...

Jul 20, 2019 | Blogging, Business, Cybercrime, Cybersecurity, CyberTraining, data sharing, Email, Employees, Facebook, Facebook, Generation-Y, Google, Hackers, Hacking, Internet, LinkedIn, LinkedIn, Malware, Monitoring, Pinterest, Privacy, Radio Show, Radio_Show, Social Media, Social Networking, Technology, Tracking, Twitter, Twitter, YouTube
Are you or your employees giving away the keys to your kingdom? The magnetism of Social Media If you have teens and you will understand the magnetism that social media seems to have over them. However, it is not only teens, but almost our entire society is...