Oct 26, 2019 | Applications, Best Practices, Business, Cyber breaches, Cybercrime, Hackers, Hacking, Patches, Patching, Radio Show, Radio_Show, Security, Security, Security Alerts, Technology, Updates, Updates
Just because you download an app does not mean that it is not vulnerable to exploit or data leaks. The chance of it happening is even higher for those not in traditional app stores. Additionally, businesses depend on older software applications are at a great risk...

Oct 26, 2019 | Audit Logs, audit logs, Best Practices, Business, Computers, Cyber breaches, cyberattacks, Cybercrime, Data Storage, Hackers, Hacking, Hacking, Patching, Privacy, Radio Show, Radio_Show, Security, Security, Third-Party, Updates
Exploitable Vulnerability Allows Major VPN Breaches 3000 Servers hacked, the blame is being pointed at a third-party provider utilizing a remote management system in the data center. Who owned the data center? That would be NordVPN, a popular consumer VPN provider....
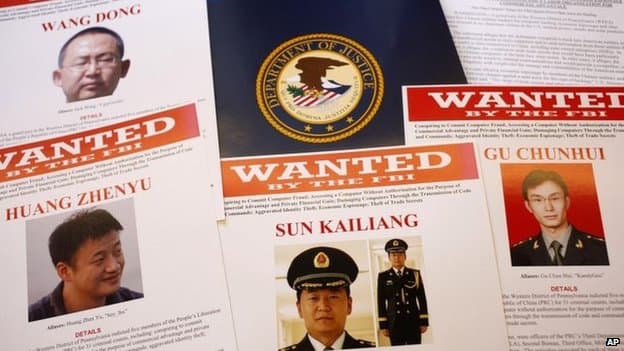
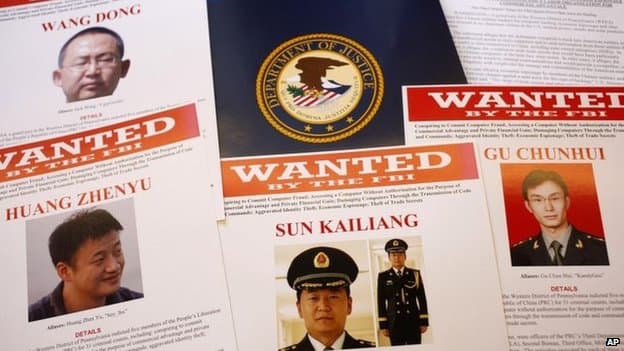
Oct 26, 2019 | Best Practices, Big Tech, Business, China, Contractors, cyberattacks, Cybercrime, Cybersecurity, Employees, Employment, Government, Guests, Hackers, Hacking, Hacking, Hacking, industrial espionage, Insider Threat, Intellectual Property Theft, Jobs, Nationstates, Radio Show, Radio_Show, Security, Security, Technology
Chinese Using Visas to Import Corporate Spys and Thieves It is about time that some of these Nation-State cyber hackers are going to prison for stealing intellectual property from our US Companies and government contractors. If you are not aware the Chinese...

Oct 19, 2019 | automation, bluetooth, Business, Consumer, cyberattacks, Cybercrime, gadgets, Hackers, Hacking, Hacking, Hacking, Hacks, Infosec, Intellectual Property Theft, Internet, IoT, Monitoring, Nationstates, Organized Crime, Passwords, Patching, Radio Show, Radio_Show, Security, Security, Security Alerts, Smart Home, spying, Surveillance, Technology, Updates
Convenience Gadgets – Design, Functionality then Security The first half of this year has been marked with a rampant increase on all those little gadget devices known by the acronym, IoT. These are any small device or controller that is network connected....

Oct 19, 2019 | Apple, Audio, Cell Phone, cell phones, Consumer, Hackers, Hacking, Hacking, Internet, iOS, iPhone, Jailbreak, Malware, Mobile, Mobile Phones, Phone, Radio Show, Radio_Show, Security, Security, Smart Phone, Technology
Fake iPhone Jailbreak Site leads to Advertising Click Fraud Jailbreaking your iPhone is never a good idea. The Apple ecosystem comes embedded with security foremost in mind, and if a problem does occur, the resolution is quick, and the patches sent to devices....

Oct 19, 2019 | Anti-Virus, Applications, Best Practices, Business, Cybercrime, Cybersecurity, Hackers, Hacking, Malware, Microsoft, Microsoft, Nationstates, Operating Systems, Organized Crime, Radio Show, Radio_Show, Security, Security, Technology, Web Tools, Windows (Microsoft)
New Tools Keep CyberThieves From Disabling Your Cyber Protections Cybercriminals are continually working to defeat any cybersecurity protections we can think up, and it happens almost as fast as we make them. Many times the malware they create has one purpose,...