Apr 9, 2021 | Agencies, Android, Android, App Store, Apple, Apple, Apps, Apps, Attack Vectors, Automation, Automotive, Best Practices, Big Data, Big Tech, Business, Cloud, Cloud Vendors, Computers, Contractors, Cryptocurrency, Cryptocurrency, cyberattacks, Cybercrime, Data Aggregator, Data Brokers, Data Loss, data sharing, Databases, Demonetize, Facebook, Facebook, Financial, Google, Google, Google Play Store, Government, Government, Hackers, Hacking, Hacking, Homeland Security, ID Theft, Internet, iPad, Malicious Insider, Malware, Malware, Mobile, Mobile Phones, Networking, News, NFTs, Patching, Phone, Pixel, Podcast, Radio Show, Radio_Show, safety, Security, Security, Security Alerts, Show Notes, Spyware, Surveillance, Tablet, Technology, Technology, Third-Party, United States, Unsecured, Updates, Valuations, vehicles, VPN, VPN, Vulnerabilities
Read. Learn. Share. Tech Talk Show Notes April 11, 2021 DHS Preparing to Use Private Contractors to “Scour Public Data and Social Media” To Compile Dissident Citizens for Watch List and No Fly Lists The U.S. Department of Homeland Security is now getting ready to...

Apr 27, 2020 | Asset Management, Backup, Business, Business Email Compromise, CEO, Compliance, Computers, Corporate Reputation, Cyber Liability, cyberattacks, Cybercrime, Cybersecurity, Cybersecurity Professional, Data Assets, Data Loss, Data Storage, Disaster Recovery, Employees, Employment, Employment, Executives, Firewalls, Hacking, Hard Disks, Hiring, Incident Response, Intellectual Property Theft, Intricate Data Systems, IT Professional, Laptops, Legacy Systems, Managed Security Services Provider (MSSP), Networking, Patching, Ransomware, Routers, Security, Security Alerts, Shadow-IT, Software As A Service, Technology, Technology, Third - Party, Updates, VPN
Overcoming the Critical Cybersecurity Talent Shortage Businesses are in Crisis mode, and it is going to get worse. Currently have more open cybersecurity jobs available than we have people to fill them, and these numbers will continue to expand in the years ahead. And...

Feb 15, 2020 | Access Controls, Applications, Artificial Intelligence, Asset Management, Attack Vectors, Audit Logs, Business, Business Email Compromise, China, Cloud, Cloud Vendors, Compliance, Corporate Reputation, credential stealing, Cyber breaches, Cyber Liability, cyberattacks, Cybercrime, Cybersecurity, Data Assets, Data Storage, Economic Disruption, Employees, Executives, Extortion, Government, Hackers, Hacking, Intellectual Property Theft, Internet, Intricate Data Systems, Legacy Systems, Malware, Managed Services Provider (MSP), Market Value, Nationstates, News, Patching, Phishing, Policies and Procedures, Radio Show, Regulatory Compliance, Security, Security Alerts, Smishing, Social Engineering, Technology, Third - Party, third-world, Updates, Vishing
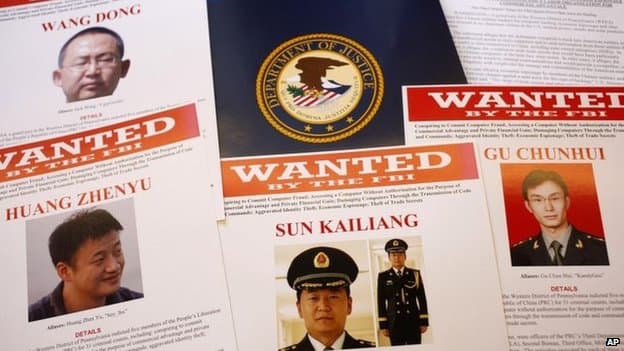
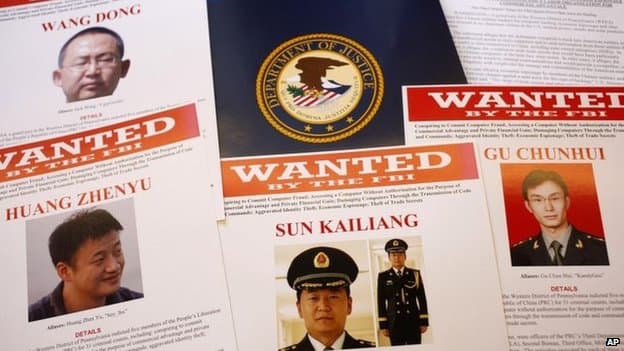
Extensive US Intellectual Property theft by Chinese being investigated by FBI Intellectual theft is a huge problem in the US and the largest perpetrator is the Chinese government. They target military sub-contractors and sub-sub-contractors, universities,...
Nov 23, 2019 | Business, Computer Repair, Computers, Disaster_Preparedness, Employment, Facebook, Google, Internet, Internet Service Providers, LinkedIn, Managed Security Services Provider (MSSP), Managed Services Provider (MSP), Networking, Operating Systems, Privacy, Radio Show, Radio_Show, Remote Repair, Security, Technology
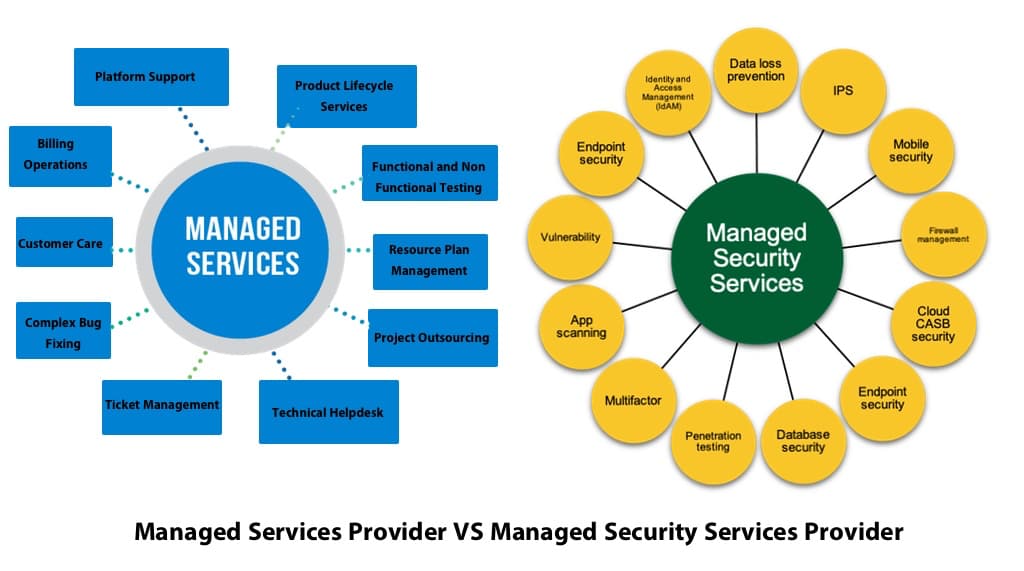
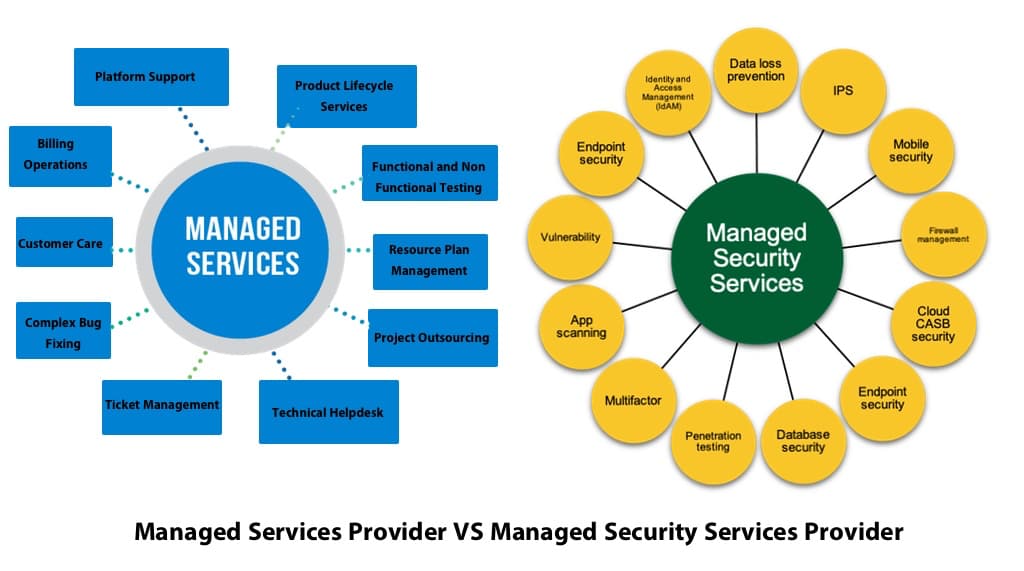
The hanging of an MSP “Shingle” and Your Business Security Are you in the cross hairs of hackers? How can a hacker multiply his efforts? By attacking a company who protects other companies. Hackers new targets are the Managed Services providers (MSPs) because...

Nov 9, 2019 | Best Practices, Business, Computer Repair, Contractors, Cybersecurity Professional, CyberTraining, Employees, Employees, Employment, Future Workforce, Internet, IT Professional, Psychology, Radio Show, Radio_Show, Security, Security, Stress, Technology
Job Dissatisfaction is prominent among IT Security Professionals Many Cybersecurity professionals love a challenge. They do not enjoy the doldrums of make work security. They long for excitement and challenging work. They are in demand so it is not suprising...
Oct 26, 2019 | Best Practices, Big Tech, Business, China, Contractors, cyberattacks, Cybercrime, Cybersecurity, Employees, Employment, Government, Guests, Hackers, Hacking, Hacking, Hacking, industrial espionage, Insider Threat, Intellectual Property Theft, Jobs, Nationstates, Radio Show, Radio_Show, Security, Security, Technology
Chinese Using Visas to Import Corporate Spys and Thieves It is about time that some of these Nation-State cyber hackers are going to prison for stealing intellectual property from our US Companies and government contractors. If you are not aware the Chinese...