Feb 29, 2020 | Asset Management, Best Practices, Business, Cable Companies, Cloud, Cloud Vendors, Computers, Cyber breaches, Cyber Insurance, Cybercrime, Cybersecurity, CyberTraining, Data, Data Assets, Data Brokers, data sharing, Data Storage, Databases, Domain Name Service, Email, Employees, Executives, Financial, Future Workforce, Generation-Y, Hackers, Hacking, Hacks, Incident Response, Information Technology, Insider Threat, Internet, Internet Service Providers, IoT, Jobs, Liability, Machine Learning, Malware, Malware, MFA, Nationstates, Networking, Open Source, Organized Crime, Password Managers, Passwords, Phishing, predictive algorithms, Radio Show, Radio_Show, Ransomware, Regulation, Regulatory Compliance, Security, Security, Security Assessments, Shadow-IT, Software As A Service, Technology, Technology, Unsecured, Web Tools, Zero-Day
All Businesses are Tech Businesses – Like it or Not The world of information is remaking businesses with new technologies turning all businesses into technology companies like it or not. Companies who continue to believe that they are not technology companies...

Jan 11, 2020 | Access Controls, Amazon, Apple, Asset Management, Attack Vectors, audit logs, Backup, Big Tech, Business, Computers, Cyber breaches, Cybercrime, Cybersecurity, Data, Data Assets, data sharing, Data Storage, Employee Training, Employment, Encryption, Fines and Penalties, Google, Hacking, Incident Response, industrial espionage, Insider Threat, Internet, Jobs, Legal, Liability, Malware, Malware, Microsoft, Monitoring, Networking, predictive algorithms, Radio Show, Radio_Show, Ransomware, Security, Software As A Service, Surveillance, Technology, Zero-Day
How Mature is Your Insider Threat Intelligence? Are insiders a threat to your business? How would you know? Today it is necessary for companies to establish a robust insider threat program that can detect employee-created risk and respond accordingly but keeping...
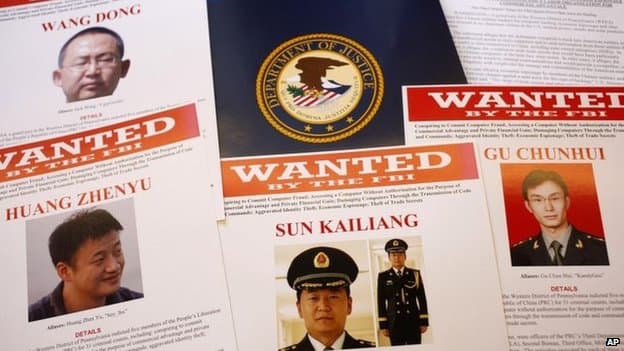
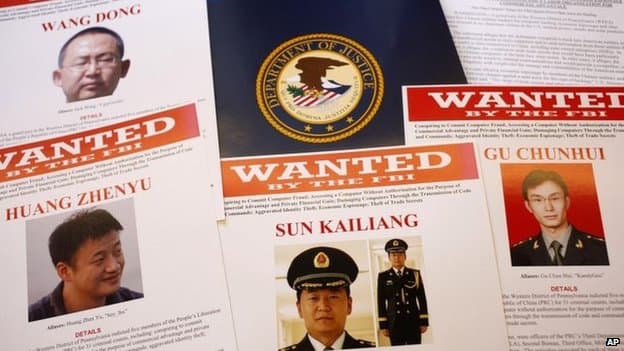
Oct 26, 2019 | Best Practices, Big Tech, Business, China, Contractors, cyberattacks, Cybercrime, Cybersecurity, Employees, Employment, Government, Guests, Hackers, Hacking, Hacking, Hacking, industrial espionage, Insider Threat, Intellectual Property Theft, Jobs, Nationstates, Radio Show, Radio_Show, Security, Security, Technology
Chinese Using Visas to Import Corporate Spys and Thieves It is about time that some of these Nation-State cyber hackers are going to prison for stealing intellectual property from our US Companies and government contractors. If you are not aware the Chinese...

Oct 5, 2019 | Business, Civilian Employment, Contractors, Cybersecurity Professional, Employment, IT Professional, Jobs, Military, Radio Show, Radio_Show, Technology, Under Arrest
Terminated Government Contractor Ends Up in Jail After Destroying IT System Resources IT people are hard to come by and are getting harder to find. That goes for business and government alike. In late 2016 the government terminated a contract with an IT Systems...

May 25, 2019 | Business, Education, Jobs, Radio Show, Radio_Show, WGIR
Guess what College Grads, your not in Kansas anymore? There are no safe spaces, and competition is the name of the game. As you reach up and grab the corporate ladder that first rung may be a real reach. Right now, the U.S. is experiencing one of the most robust job...