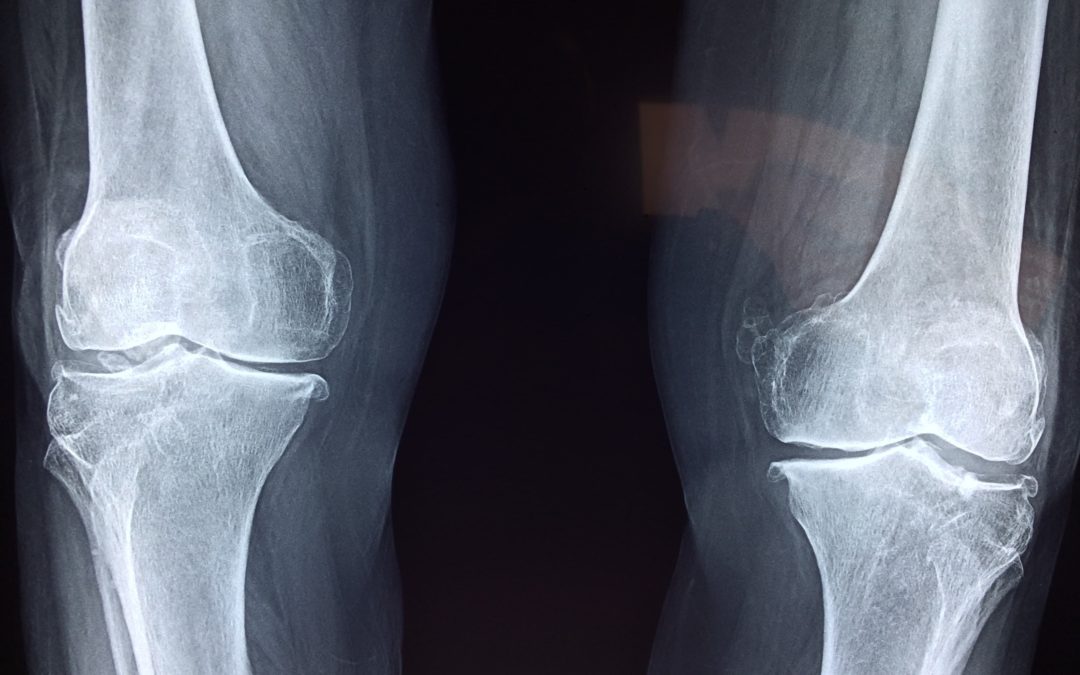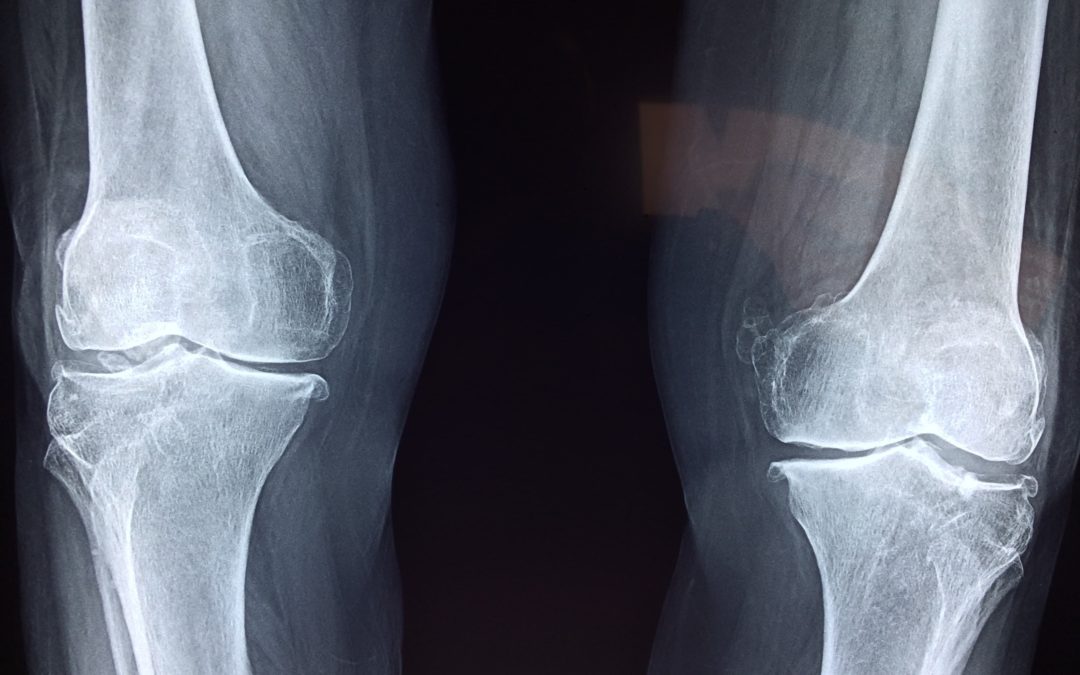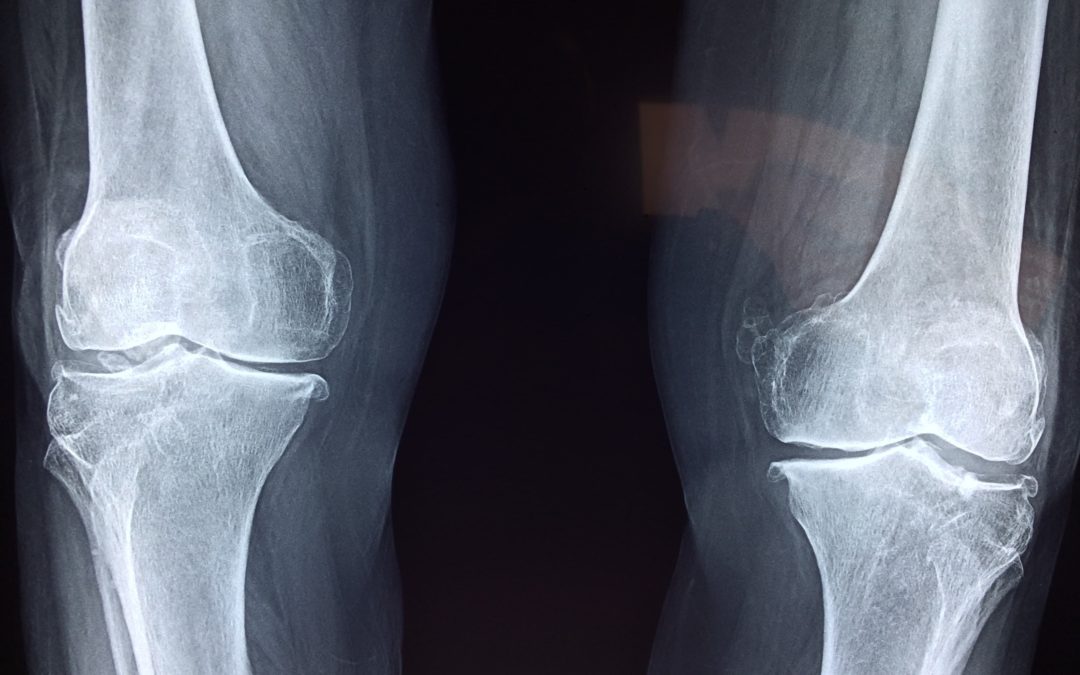
Oct 5, 2019 | Artificial Intelligence, Artificial Intelligence, Artificial Intelligence, Big Tech, Computers, Data Storage, Databases, Health, Images, Machine Learning, Radio Show, Radio_Show, Software, Technology, X-ray
FDA Approves New X-ray Technology System That Implements Machine Learning Algorithms. Artificial Intelligence is coming to a hospital near you. Well, not exactly. What we have is machine learning, and it is a precursor to real artificial intelligence. Machine learning...

Sep 28, 2019 | Best Practices, Business, Government, Insider Threat, Radio Show, Radio_Show, Security, Security, Technology
Insider Threats and DoD Response Insider threats are a danger to every organization. While all threat actors have motives, insiders enjoy ideal means and opportunity. From the inside, they are in a much better position to carry out damaging activities....

Sep 28, 2019 | Civilian Employment, Cybercrime, Databases, DOD, Internet, Military, Radio Show, Radio_Show, scam, Technology, Veterans
Cybercriminals Target Veterans Looking for Civilian Employment Taking advantage of anyone is unacceptable. However, when it targets our warriors who are seeking civilian employment at the end of their military service, I find it infuriating. Cybercriminals set up an...

Sep 27, 2019 | Best Practices, Business, Data Storage, Hacking, Hard Disks, Hard Disks, Hardware, industrial espionage, Legal, Radio Show, Radio_Show, Recycling, Security, storage, Technology
Recycling Disks the Wrong Way can Bite you! Recycling old technology is big business. Companies employ life cycle management for their IT hardware. Disposing of used servers, storage, and networking equipment on your own can be expensive and time-consuming and often...

Sep 27, 2019 | Audit Logs, Business, Coding, cyberattacks, Cybercrime, Cybersecurity, data sharing, Databases, Governance, Hacking, Nationstates, Organized Crime, Radio Show, Radio_Show, Security, Security Alerts, Technology
Audit Logs May Help You Make Your Case — If You Have Them Most businesses today are fielding malicious attacks on a daily and sometimes hourly basis. Do you keep audit logs of the activity on your computer system? Logs can act as a red flag to identify when...

Sep 27, 2019 | DeepFake, Images, Machine Learning, Media, Radio Show, Radio_Show, scam, Technology, Video
Real or Fake — Can You Tell Perfect “Deep Fakes” in the Next Year DeepFakes can appear as Videos or Images, and it is getting harder to tell if they are real. Gone are the days of tabloids who put a famous face on a not so great body and it was pretty easy to know...