Feb 15, 2020 | Access Controls, Applications, Artificial Intelligence, Asset Management, Attack Vectors, Audit Logs, Business, Business Email Compromise, China, Cloud, Cloud Vendors, Compliance, Corporate Reputation, credential stealing, Cyber breaches, Cyber Liability, cyberattacks, Cybercrime, Cybersecurity, Data Assets, Data Storage, Economic Disruption, Employees, Executives, Extortion, Government, Hackers, Hacking, Intellectual Property Theft, Internet, Intricate Data Systems, Legacy Systems, Malware, Managed Services Provider (MSP), Market Value, Nationstates, News, Patching, Phishing, Policies and Procedures, Radio Show, Regulatory Compliance, Security, Security Alerts, Smishing, Social Engineering, Technology, Third - Party, third-world, Updates, Vishing
Extensive US Intellectual Property theft by Chinese being investigated by FBI Intellectual theft is a huge problem in the US and the largest perpetrator is the Chinese government. They target military sub-contractors and sub-sub-contractors, universities,...
Jan 11, 2020 | Applications, Artificial Intelligence, Asset Management, Attack Vectors, Audit Logs, audit logs, Backup, Business, CEO, Cloud, Cloud Provide, Cloud Vendors, Compliance, Computers, Cyber breaches, Cyber Insurance, Cyber Liability, cyberattacks, Cybercrime, Cybersecurity, Cybersecurity Professional, Data, Data Assets, data sharing, Data Storage, Databases, Employees, Fines and Penalties, Government, Hacking, Hacking, Incident Response, Incident Response, industrial espionage, Intellectual Property Theft, Internet, Machine Learning, Malware, Managed Security Services Provider (MSSP), Microsoft, Networking, Operating Systems, Patching, predictive algorithms, Radio Show, Radio_Show, Security, Security Alerts, Software As A Service, Technology, Third - Party, Updates, Vulnerabilities
Cloud Migration Considerations to Take into Account Deciding to move to business technology services to “the Cloud” is one of the most significant that is made by business leaders, and it is a decision best not made without the approval at the highest...

Nov 9, 2019 | Applications, Artificial Intelligence, Audit Logs, Best Practices, Business, credentials, Cyber breaches, cyberattacks, Cybercrime, CyberTraining, data sharing, Data Storage, Databases, Employees, Employees, Firewalls, Firewalls, Hackers, Hacking, Hacking, Hacks, Hard Disks, Intellectual Property Theft, Laptops, Liability, Malware, Malware, Networking, Networking, Patching, Radio Show, Radio_Show, Ransomware, Routers, Security, Security, Security Alerts, segmentation, Software As A Service, Switches, Technology, Updates
Cyberbreaches cause Small Businesses to Close Cybercriminals have found a lucrative new target – the small business. Unfortunately, for a tenth of them the breach meant closing their doors forever. The impacts on small businesses is excentuated greatly....

Oct 12, 2019 | Alexa, Applications, Artificial Intelligence, Artificial Intelligence, automation, Big Tech, Business, Cars, Consumer, Data, Infosec, Phone, Radio Show, Radio_Show, Security, Siri, Smart Assistants, Technology
The Future Communication Means No Phones Our world today is changing, and we are demanding convenience, efficiency, and speed in our transactional pursuits, and this might mean that smartphone you purchase or finance for the next five years might be unnecessary...
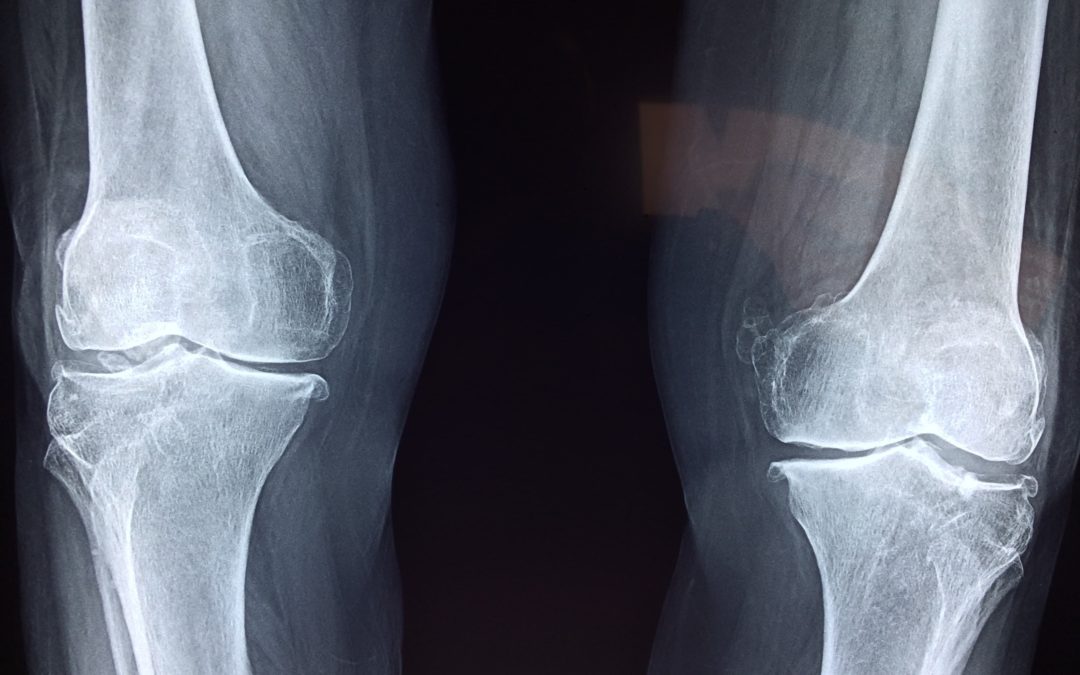
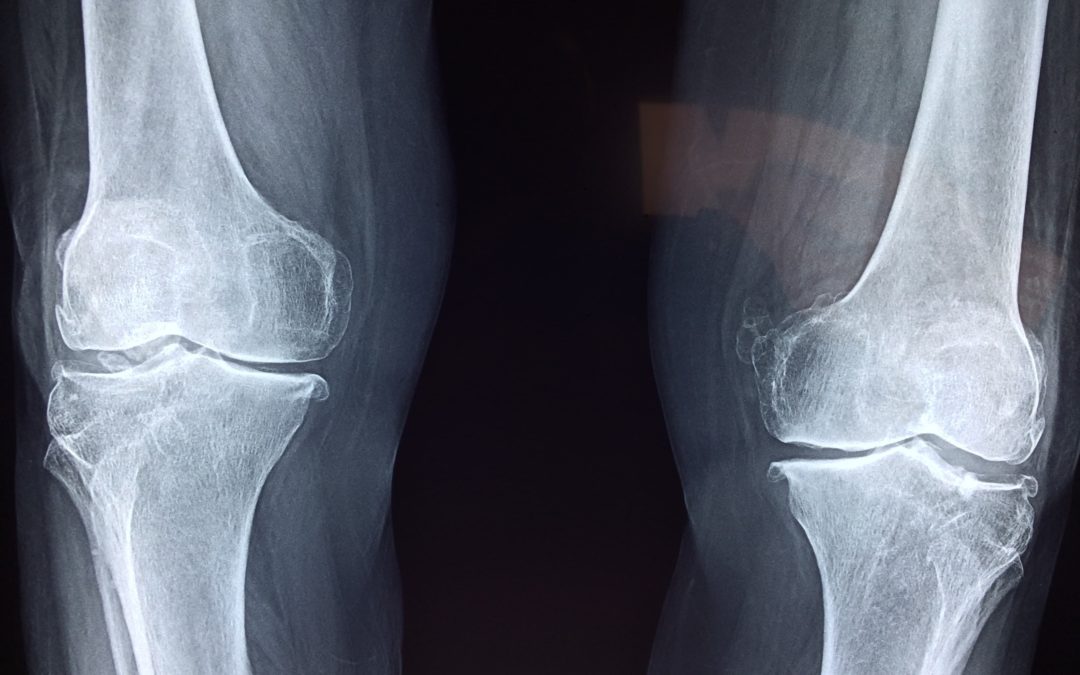
Oct 5, 2019 | Artificial Intelligence, Artificial Intelligence, Artificial Intelligence, Big Tech, Computers, Data Storage, Databases, Health, Images, Machine Learning, Radio Show, Radio_Show, Software, Technology, X-ray
FDA Approves New X-ray Technology System That Implements Machine Learning Algorithms. Artificial Intelligence is coming to a hospital near you. Well, not exactly. What we have is machine learning, and it is a precursor to real artificial intelligence. Machine learning...

Jun 29, 2019 | Artificial Intelligence, Artificial Intelligence, Computers, Cybersecurity, Education, Hacking, Radio Show, Radio_Show, Security, Software, Technology
We Will Need 3.5 Million Cybersecurity Professionals by 2021 and They Won’t Come Out Of Our Colleges Unfilled cybersecurity jobs are expected to reach 1.8 million by 2022, up 20% from 1.5 million in 2015, according to the Center for Cyber Safety and...