
The Road To Machine Learning Wars
The Road To Machine Learning Wars How we fight wars is changing and changing in a big way. With the advancement of technology, conducting our battles will be done with speed and accuracy unavailable today, and we will be facing wars driven by machine learning...

Upping your Incident Response Game — New Regulations coming
Upping your Incident Response Game -- New Regulations coming If you are a business and you have data on any Massachusetts resident or do business in Massachusetts, coming in early January, there are new data collection requirements with which you will need to...

Why Zero Trust Is the Answer to Internet Everywhere Connections
Why Zero Trust Is the Answer to Internet Everywhere Connections Everyone everywhere has a mobile device, and connections to the internet are available whenever we want it. In our connected world, it means that keeping your businesses secure means fighting a...

Cybercriminals return to old-school ID theft tactics
Cybercriminals return to old-school ID theft tactics As security professionals come up with new protocols and software to protect companies and businesses implement them, hackers are finding themselves thwarted. So many of these cybercriminals are going...

Reduce Vulnerabilities by Ditching Android
Reduce Vulnerabilities by Ditching Android Like I repeatedly explain to people to ask me about Android. Android is not Android is not Android. Every Android phone is unique because the Manufacturers are allowed to freely create applications and interfaces and...

Big Data, Data Brokers and Your Information
Big Data, Data Brokers and Your Information Big Data brokers collect our data and establish “hidden” ratings about us before selling it to those who will pay. This information is used by marketers, insurance companies, credit companies, and merchants. ...

Tackling Ransomware on Windows
Tackling Ransomware on Windows Microsoft has 1 billion Windows-OS powered PCs in use worldwide which explains why they are such a big target for hackers. There are a number of Windows security threats that everyone needs to be aware of including potentially...
Cellular Throttling and Why it cost AT&T a Chunk of Change
Cellular Throttling and Why it cost AT&T a Chunk of Change We are all familiar with cell carriers and their different plans -- some of which seem to change as fast as the weather in New England. All of them have some type of an ulimited plan -- but the...
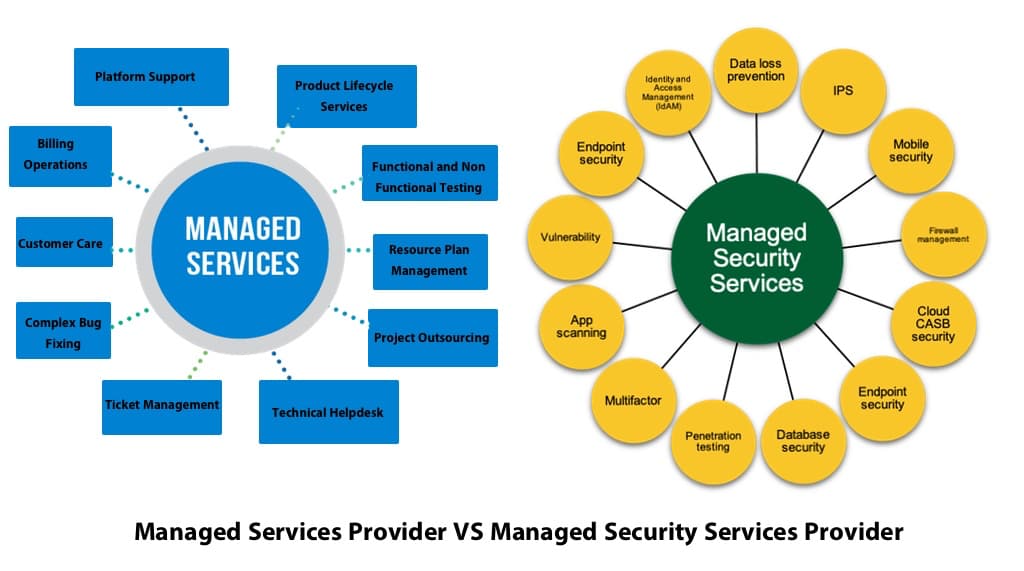
The hanging of an MSP “Shingle” and Your Business Security
The hanging of an MSP “Shingle” and Your Business Security Are you in the cross hairs of hackers? How can a hacker multiply his efforts? By attacking a company who protects other companies. Hackers new targets are the Managed Services providers (MSPs) because...

