Oct 26, 2019 | Best Practices, Big Tech, Business, China, Contractors, cyberattacks, Cybercrime, Cybersecurity, Employees, Employment, Government, Guests, Hackers, Hacking, Hacking, Hacking, industrial espionage, Insider Threat, Intellectual Property Theft, Jobs, Nationstates, Radio Show, Radio_Show, Security, Security, Technology
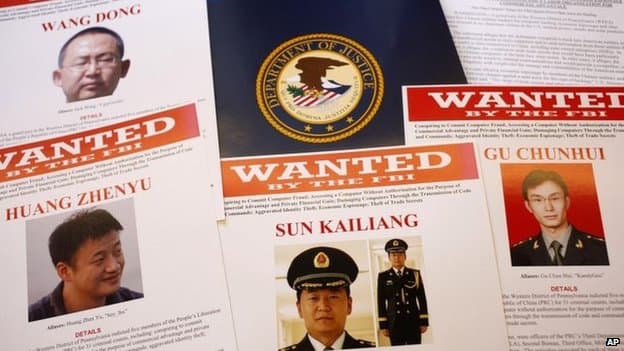
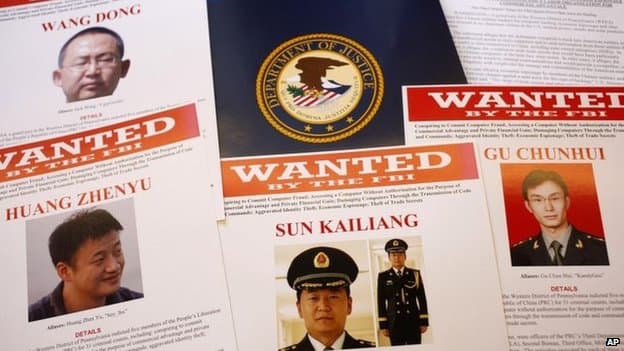
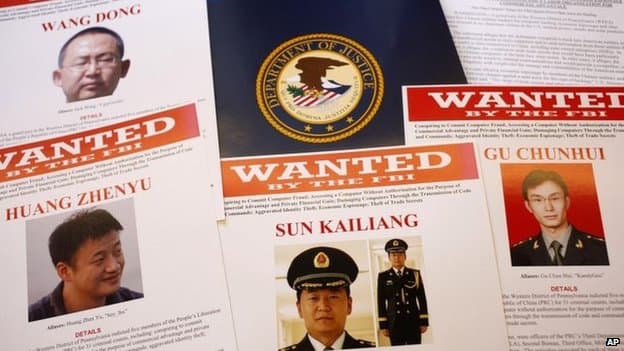
Chinese Using Visas to Import Corporate Spys and Thieves It is about time that some of these Nation-State cyber hackers are going to prison for stealing intellectual property from our US Companies and government contractors. If you are not aware the Chinese...

Oct 19, 2019 | Aviation, Business, China, Cybercrime, FAA, Financial, Government, Hackers, Hacking, industrial espionage, Intellectual Property Theft, Liability, Marketplace, Nationstates, Patents, Politics, Radio Show, Radio_Show, Security, Technology, Transportation, Uncategorized
Nation-State Cybertheft May Cause US Aerospace Downfall Our government leaders have known for years about the industrial espionage conducted by China. It is at the expense of our American companies. They know of China’s goal to develop a colossal aerospace...

Oct 12, 2019 | Best Practices, Business, Cyber breaches, cyberattacks, Cybercrime, Cybersecurity, Hackers, Hacking, Hacks, industrial espionage, Internet, Malware, Radio Show, Radio_Show, Security, Security, Technology
More Than Three-Quarters of US Businesses Are CyberAtttack Targets Cybersecurity incidents are up! Hackers worldwide favorite target du jour are U.S. small and medium-sized businesses. Unfortunately, for many, they have fallen back on the false idea they are...

Sep 27, 2019 | Best Practices, Business, Data Storage, Hacking, Hard Disks, Hard Disks, Hardware, industrial espionage, Legal, Radio Show, Radio_Show, Recycling, Security, storage, Technology
Recycling Disks the Wrong Way can Bite you! Recycling old technology is big business. Companies employ life cycle management for their IT hardware. Disposing of used servers, storage, and networking equipment on your own can be expensive and time-consuming and often...

Sep 23, 2019 | Best Practices, Business, Cyber breaches, cyberattacks, Cybercrime, Email, Hacking, Hacking, industrial espionage, Nationstates, Organized Crime, Phishing, Privacy, Radio Show, Radio_Show, Ransomware, Ransomware, Ransomware, scam, Security, Security, spying, Technology
Saudi IT Providers Hit in Cyber Espionage Operation In what appears to be a coordinated and targeted cyber espionage campaign, the networks of several major IT providers in Saudi Arabia were attacked in the past year as a stepping-stone to the attackers’...